According to a Forbes article from February 2022, 25% of all professional jobs in North America will be remote by the end of the year. Companies realize that remote work is here to stay, and are looking into permanent solutions to the challenge of providing easy access to all employees while maintaining consistent data security across all assets.
Table of contents
- What is a software defined perimeter (SDP)?
- What is the purpose of a software defined perimeter?
- What is the difference between software-defined perimeter and zero trust?
- What is a VPN?
- How does a VPN work?
- How is SDP different from VPN?
- What are some disadvantages of a traditional VPN compared to an SDP?
- Is GoodAccess a VPN or an SDP?
The traditional approach has been to use a legacy virtual private network (VPN) to secure remote user and branch connections. However, a VPN may possess certain security vulnerabilities and manageability issues that more recent technologies, such as zero trust network access and software defined perimeter, eliminate.
This article covers several topics to give you a thorough understanding of differences between a software-defined perimeter and a virtual private network. What is SDP and VPN? What is the difference between software-defined perimeter and zero trust? What are they used for? Let's start with the basics and break these questions down.
What is a software defined perimeter (SDP)?
The software defined perimeter (SDP) is a networking model that imports business network security into virtual and cloud deployments.
It was developed as a response to the shortcomings of the traditional network security approach that centers on a secure exterior boundary protecting a trusted internal network. Though it has been a network security staple for decades, it copes poorly with securing remote access to internal systems and connections to cloud resources, and the SDP addresses this.
What is the purpose of a software defined perimeter?
The software-defined perimeter rejects the idea of a perimeter altogether and instead focuses on establishing one-to-one connections on a per-session basis. The purpose of doing this is to mask online activity and reduce potential attack opportunities for cybercriminals.
Because the perimeter is so blurred and the SDP does not functionally distinguish between internal and remote systems, it draws no distinction between on-site and remote users, either. It validates all connection attempts equally (with exceptions such as adaptive authentication), making it very well-suited for the distributed IT infrastructures of contemporary companies.
What is the difference between software-defined perimeter and zero trust?
SDP is often mentioned in tandem with zero-trust network access (ZTNA), which is another network security model that does not grant free network access but only allows access to selected systems for satisfactorily authorized users.
So is SDP a zero trust? Though each approach has a different history, in practical terms, SDP and ZTNA can be considered synonymous—they both enhance security by minimizing the implicit trust zone and emphasizing strong encryption and robust, identity-based user authentication.
Both software-defined perimeter and zero trust network access have to balance security with user experience, neither of which should be at the expense of the other. A successful implementation of each model, therefore, invariably includes
- access control mechanisms
- identity management techniques; i.e., single sign-on (SSO) or multi-factor authentication (MFA) as a bare minimum.
For more information on SDP, check out this blog post.
What is a VPN?
A VPN, or virtual private network, is a technology that securely and privately connects users or devices to other resources, whether a website, a cloud system/application, or an on-site system.
In terms of company network security, VPNs can endow the traditional physical-boundary security model with secure remote access capabilities. IT admins can configure an entry point, e.g. a router or a firewall, to serve as a VPN gateway or even deploy a dedicated VPN server to manage remote user connections. Learn more about the usage of VPN in a business environment.
How does a VPN work?
The VPN creates a hidden network of servers, routers, and other devices to allow users to connect to them remotely and securely. Authentication to a VPN traditionally happens on the network level, which means both the user and their device are verified.
VPNs use several protocols; OpenVPN, IPsec, and IKEv2 rank among the most common, but there is also the recent Wireguard protocol, and the older SSTP and PPTP.
There are several types of VPN out there.
Personal VPN
A personal VPN is an online tool intended for individuals. Internet users use them to escape surveillance, bypass content restrictions, or ensure data security on an unsecured network.
A downside of a personal VPN is that the user pays for access to a remote server through which they access the internet, which means their activity is still visible to the VPN provider.
Business VPN
A business VPN provides secure site-to-site connections to interconnect remote networks, and point-to-site connections to secure communications with remote or third-party workers. The infrastructure is entirely under the company’s control.
Depending on the deployment, a business VPN may require significant hardware resources and fast internet connection.
Cloud business VPN
A cloud business VPN provides the same functionality and privacy as a traditional business VPN, except delivered as a cloud service, which improves its scalability, cost-efficiency, and makes it more broadly accessible.
You could say a cloud business VPN is an intermediate step between a legacy business VPN and an SDP.
For an in-depth look into how VPNs work, check out this article.
How is SDP different from VPN?
An SDP solution can do everything a VPN can. In fact, it improves upon the security a traditional VPN provides and makes up for some of its downsides.
What are some disadvantages of a traditional VPN compared to an SDP?
The major drawback of a virtual private network solution is that once a user is authorized, they are granted more or less free network access unless very strict firewall and access control rules are in place. However, if this user is a cybercriminal in possession of legitimate user credentials, they gain free rein in the internal network with plenty of opportunities to move laterally and pursue highly sensitive targets.
On the other hand, a software defined network solution establishes user-to-system connections only after both have been authenticated; and does so per each individual session. This provides several benefits.
- Reduced attack surface because of a lack of full network access,
- Minimal risk of IP address exposure, protecting from attacks such as DDoS,
- Better user experience.
To sum up, an SDP has the functionalities of point-to-site, site-to-site, and cloud-to-site VPN bundled together for easier management and improved flexibility. It is a more robust technology that is better suited to the decentralized reality of corporate networks today.
| Legacy VPN | SDP |
|---|---|
| Network access to authorized users | Connects authorized users to authorized applications |
| Limited control and visibility | Improved visibility |
| Difficult to deploy | Easy to deploy |
| Hard to scale and manage | Easy to manage |
| Bare-bones network access | Granular access control mechanisms |
| Vulnerable to some online threats | Immune to traffic interception, invisible to DDoS attacks, protected from phishing, etc. |
Tab. 1 - SDP vs VPN: Differences between a traditional VPN and SDP
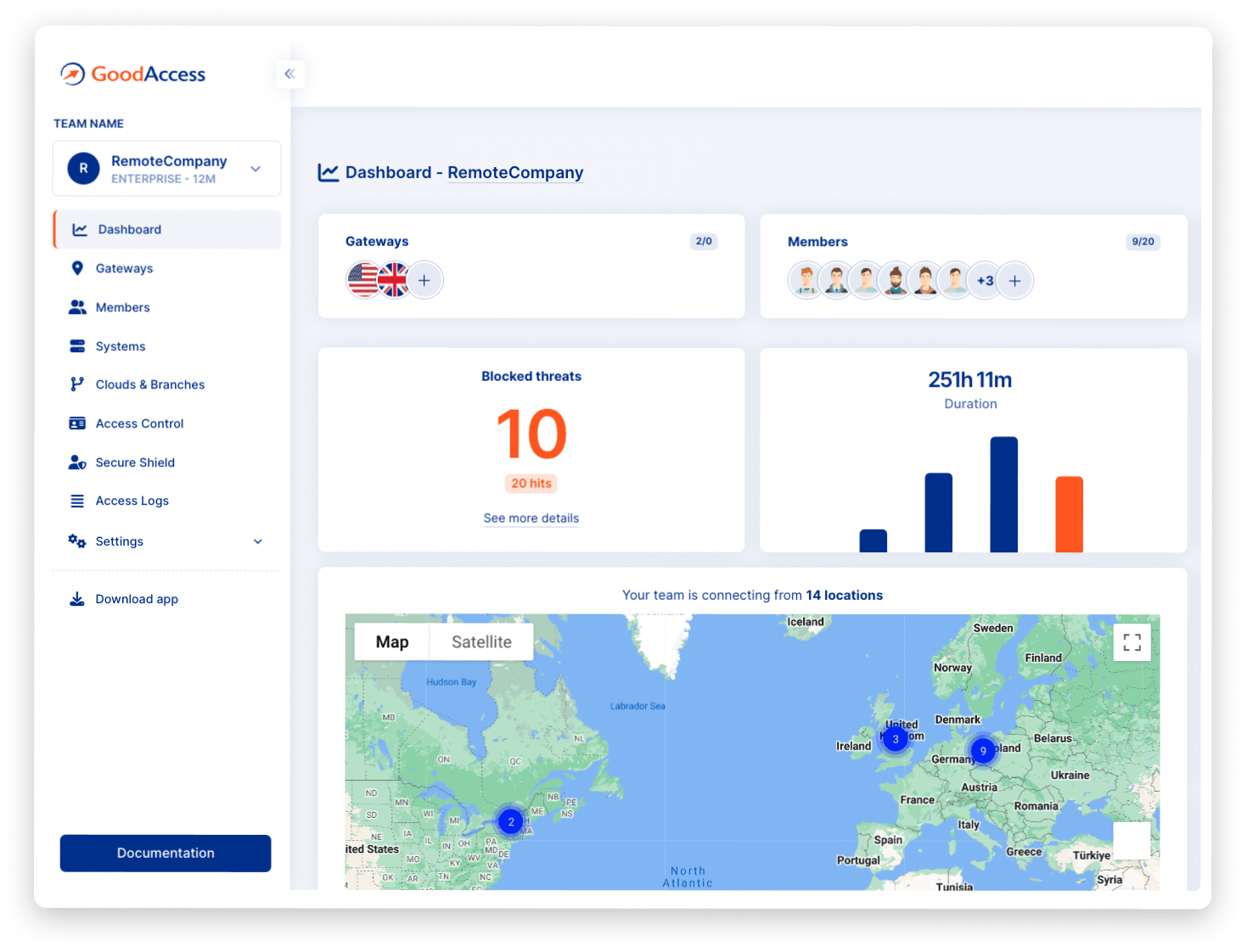
Is GoodAccess a VPN or an SDP?
Both. GoodAccess has a VPN pedigree, and offers a cloud business VPN as a large part of its service offerings, but it does much more than that.
GoodAccess is a mature cybersecurity technology providing secure remote access fully in line with the requirements of SDP and ZTNA, complete with flexible multi-cloud and multi-branch connections, granular access control mechanisms, identity obfuscation, innate threat protection, and more.
If you aren’t a GoodAccess user and would like to build a software-defined perimeter in under 10 minutes, start by creating a free account.