How DNS Filtering Can Help Secure Your Business
DNS filtering is a security technique that protects against malware by blocking access to malicious sites. It is a kind of automated access control that allows companies to protect against data theft and prevent harmful content from being downloaded to user devices.
Key Terms
- Malware: Software that is intentionally designed to interfere with computer security to cause disruption and steal information.
- Ransomware: A type of malware that threatens to publish private data online or blocks access to your data until a ransom is paid.
- Domain: A name that identifies services on the Internet, such as a website. Every website has a domain name.
- Domain name system (DNS): A naming system for computers, services, and other resources on the Internet.
- IP address: A unique code assigned to a device when it connects to the Internet.
- Ransomware: A type of malware that threatens to publish private data online or blocks access to your data until a ransom is paid.
- Phishing: Phishing attacks are when a cybercriminal sends someone a fake email or text message with a link that takes them to a malicious website. Usually, they will be asked to enter login details—which is how a hacker would steal usernames and passwords—or to download something that ends up being malware.
- Command-and-control (C&C) server: A computer that is controlled by a cybercriminal that is used to send commands to a system infected with malware. It also receives any data from the network that the malware attacks.
What is DNS Filtering?
DNS filtering, also known as DNS blocking, is a security technique based on blocking access to malicious, disreputable, or otherwise unwanted domains.
➡️ It is the same as only giving employees access to certain external doors to enter a building.
When a user tries to access a domain, the query is compared to a blacklist of unwanted domains or IP addresses, and if there is a match, the domain will not be resolved and access blocked.
➡️ Just like if they tried to access via the wrong door, they would not be able to gain entry to the building.
An example of where DNS filtering can protect your business would be if one of your employees were to receive a phishing link via email sent by a cybercriminal. If they then clicked on this link, malware could be installed or they could have their credentials stolen.
If, however, the website domain for the phishing link had been blacklisted, this type of attack would automatically be blocked.
Blacklists are developed and maintained by spam detection companies and systems like the spam and open relay blocking system (SORBS).
What Does This Mean for Your Business?
👉 Employees can easily make the mistake of downloading malware or having their credentials stolen.
👉 If the website they are being directed to is on your company's blacklist, they will not be able to access it.
👉 This protects your business against any potential malware attacks or information breaches.
How does DNS filtering work?
DNS filtering involves using IP addresses to identify domains.
Let's take the domain name goodaccess.com, for example. This domain is what would be entered into your browser.
This domain name is connected to an IP address, which is a unique set of numbers. Machines will use a unique IP address to know where to send Internet traffic.
➡️ Similarly, an access-controlled building would have a list of people who are allowed into the building, and their access cards—which you can think of as IP addresses—would be programmed for specific doors only.
Before you can access websites, your device needs to retrieve the IP address for the website through something called DNS resolution.
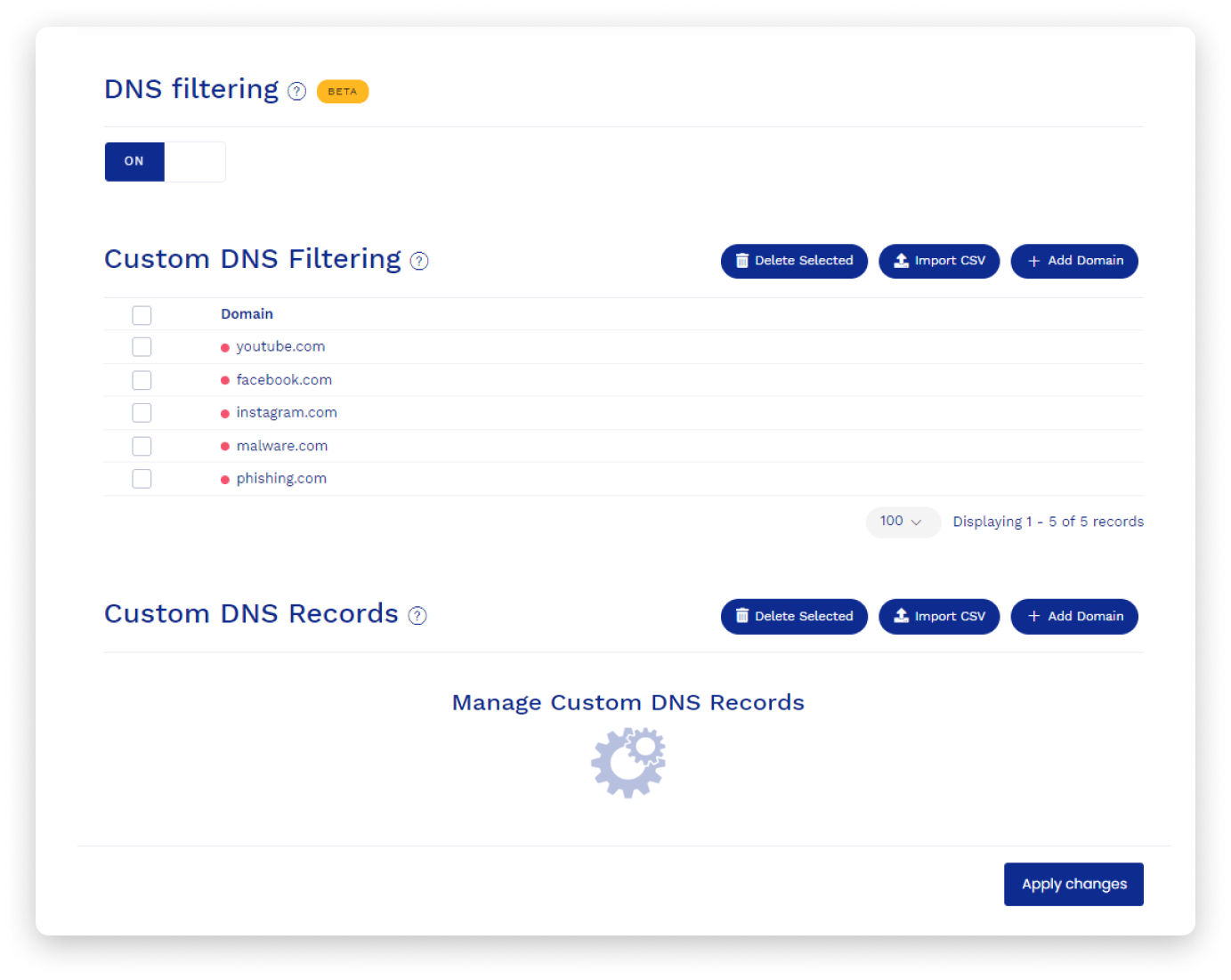
Fig 1: An example of DNS filtering settings in GoodAccess cloud VPN settings.
What Is the Domain Name System (DNS)?
DNS stands for Domain Name System. It refers to the translation of domain names to the appropriate IP addresses.
A domain name is what you see in the address bar (URL window) of your web browser; in this case it says goodaccess.com. Domain names are easy for humans to understand and remember, but machines use numerical IP addresses to know where to send traffic. This means that before you can access content on a website or an online application, your device has to retrieve the IP address via a series of steps collectively known as DNS resolution.
What is DNS resolution?
DNS resolution is how your device obtains the IP address of the server it is trying to access.
- First, it sends a DNS query to the DNS resolver, which is a service that translates domain names to IP addresses.
- The DNS resolver either looks up the domain name and sends back the corresponding IP address, or it asks other DNS servers.
- DNS resolvers keep a cache of queries and IP addresses to speed up the resolution of frequently visited domains.
- Once your device receives the correct IP address, the domain is resolved.
What is DNSSEC?
Some parts of the DNS are vulnerable. Attackers misuse DNS by "listening in" on the communication and intercepting information like email addresses, eavesdropping on phone conversations, or redirecting users to fraudulent and phishing websites.
DNSSEC, or Domain Name System Security Extensions, refers to a number of security improvements that patch up some vulnerabilities of the domain name system and protect it from misuse.
DNSSEC solves vulnerability issues by implementing asymmetric cryptography, i.e., by encrypting and decrypting the communication with a different key. This strengthens the authentication in DNS and significantly improves the security and trustworthiness of a domain.
What Does This Mean for My Business?
👉 Most of the public Internet still operates on DNS which is not secured with DNSSEC.
👉 It is a good idea that your business secures your communications with DNS filtering, especially if you have teams working remotely via the public Internet.
What is a blacklist?
In networking terms, a company's blacklist, also known as a blocklist or denylist, is a list or database of domains or IP addresses that users are not allowed to access.
➡️ This would be like a list of people who are not allowed into your building.
These blacklisted websites may be known for:
- Malware distribution.
- Sharing bootleg copies of copyrighted materials.
- Serving as C&C servers.
- Hosting adult or otherwise undesirable content.
The opposite of a blacklist/blocklist is a whitelist or allowlist.
As the name suggests, a whitelist allows access to any listed domain, even if such a domain were on a blacklist. Whitelisting is therefore reserved for highly trusted domains only.
What Is the Value of DNS Filtering for Small Businesses?
Although a DNS filtering service should not be the only solution you rely on when it comes to protecting your company data, it is still a highly effective security measure.
There are three primary use cases for DNS filtering.
Blocking malware-hosting websites
Websites that host malware can be detrimental to your business. Once your company-managed networks have been infected with malware, you can expect your operations and productivity to be completely upended.
DNS blocking is often the first line of defense against a malware infection.
Employees can be tricked or redirected to a malicious website where malware would be downloaded onto their devices.
From there, it can spread through the rest of company infrastructure and, if left unchecked, eventually cripple company operations.
This is why DNS filtering is a sensible measure to help prevent company data breaches.
Blocking phishing sites
Phishing attacks are a common way for a business's entire network to be breached. In this case, attackers try to scam your employees into giving up their login information.

Phishing protection is a related use case where attackers try to scam employees into giving up their access credentials by directing them to a legitimate-looking website asking for a password and username. These sites often look visually indistinguishable from the real ones, but their domain names and IP addresses are, of course, different.
In this sense, DNS filtering acts as a safety net for employees who may unwittingly fall for a phishing lure (read more about phishing here).
Blocking access to prohibited websites
You want your team to be as productive as possible. Sometimes, certain websites can get in the way of that productivity, which would impact your small business.
You can use DNS filtering tools to enforce your content and Internet access policies. You can do this by blocking access to the IP addresses associated with the websites you do not want your team to visit.
Here are some types of websites you may want to prevent access to within your business:
- Adult sites or adult content sharing.
- Websites that allow sharing of copyrighted content, like torrenting.
- Gambling services.
- Games websites.
Productivity-oriented companies may even choose to block social media, entertainment sites, and other distractions.

How Do You Enable DNS filtering?
There are several ways to implement DNS filtering depending on the technology you choose to carry it out. You can block access on your:
- Business VPN as part of access control.
- Firewall.
- Load balancer.
- Subscription to a DNS filtering service.
How Does GoodAccess Business VPN Implement DNS Filtering?
GoodAccess provides a DNS filtering service as part of the VPN gateway.It runs its own DNS infrastructure that handles all DNS resolutions for every connected client.
GoodAccess provides a DNS filtering service as part of the VPN gateway.It runs its own DNS infrastructure that handles all DNS resolutions for every connected client.
- Malicious sites.
- C&C servers.
- Phishing websites.
- Abuse sites.
When an employee tries to access a domain on your company's blocklist, GoodAccess does not resolve the domain but blocks the attempt, logs the activity, and redirects the user to a safe website explaining what has happened.

Fig 2: A message informing the user of a domain being successfully blocked.
If, for example, the user falls for a phishing attack, instead being prompted for login credentials, they are informed of the malicious presence on their device without any harm done.
This is an efficient way for your team admin to know when something suspicious is happening within your company-managed networks. It could be an early indication of a malware infection that needs to be removed.
If restricting access to websites that are not implicitly featured on the default blacklists is important to you and your business, you can add their domain names in GoodAccess.
You can do this manually or import your own blacklist as a CSV file. Your company's blocklist may include websites that significantly affect your team's productivity. These can also easily be added to your cloud VPN.
If you want to try out GoodAccess's DNS filtering capabilities and other remote access and security features, check out the full-featured 14-day free trial here.
