Hybrid and remote work have now firmly established themselves in the work patterns of companies all over the world. Many businesses turned to remote access VPNs to enable telework for their employees, whether as a permanent solution or a quick fix during the first covid lockdown.
This article delves into what remote access VPNs are, how they work, and what alternatives there may be.
Table of contents
1. What is a remote access VPN?
2. What are the benefits of using a remote access VPN?
3. Are remote access VPNs obsolete?
4. What are the alternatives to a remote access VPN?
5.Summary
What is a remote access VPN?
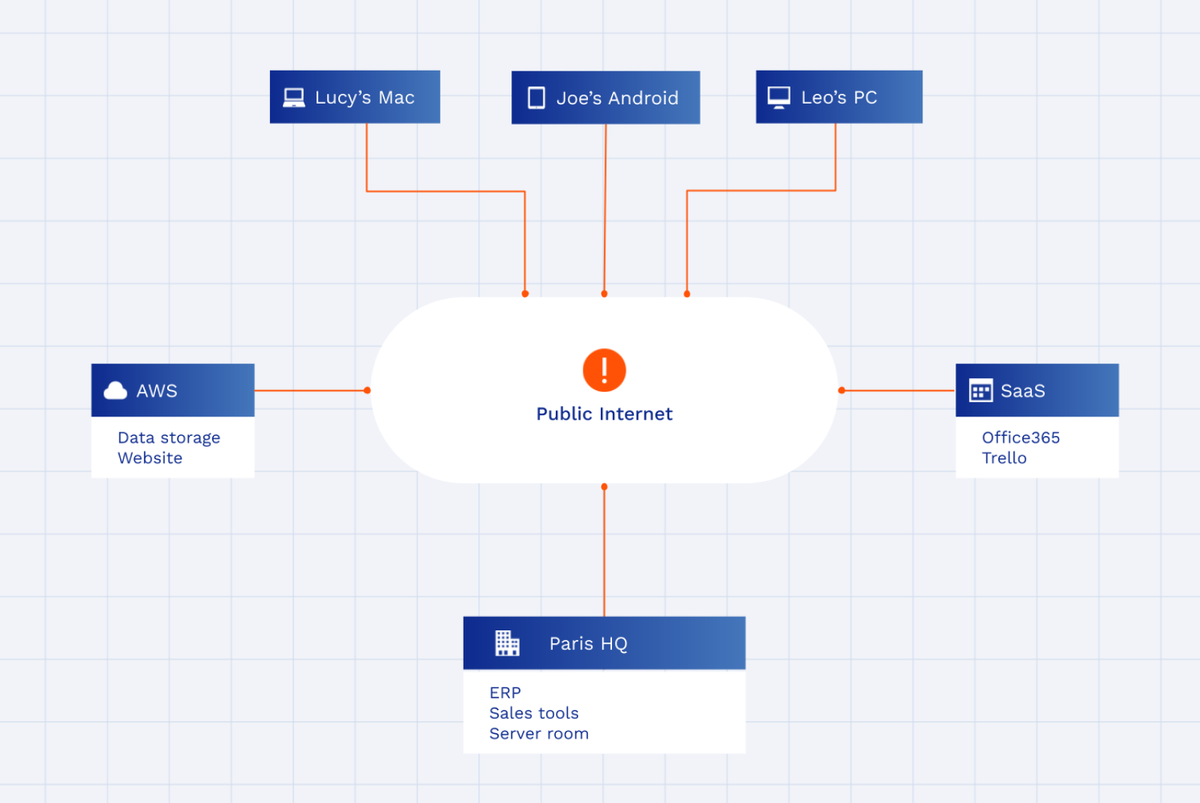
A remote access VPN is a security solution that allows employees and contractors to connect to company networks (LANs, clouds) from remote locations; e.g. from home or during travel. In this day and age a remote access VPN is a necessary component of many business IT infrastructures that provides security to company IT assets as they become increasingly distributed and decentralized, and enables them to be more easily and readily available.
Unlike a site-to-site VPN, which connects local networks (e.g. company branches), remote access VPN provides remote access to local systems for individual users. However, they are not mutually exclusive, in fact some VPN solutions provide both.
There are several deployment types of remote access VPNs:
- Hardware VPN – The VPN functionality is provided by a dedicated device or by a router or firewall configured for this purpose.
- Software VPN – A virtual VPN solution that is usually easier to manage, is more user-friendly, and costs less.
- Cloud VPN – A dedicated VPN service delivered from the cloud. It doesn’t require any underlying infrastructure from the user, eliminates the need of maintenance, and scales easily.
Some cloud VPNs also come as part of a larger service package, for example IaaS. These VPNs are easy to deploy, but they don’t come with as many features and generally serve a relatively narrow purpose. See this blog to learn more about different types of VPNs.
How does a remote access VPN work?
A remote access VPN creates an encrypted tunnel between the client and a VPN gateway/server/collector that shields all the communication within. They use VPN protocols, such as OpenVPN, IPsec, Wireguard, etc.
The VPN gateway/collector can be a network device, e.g. a router or a firewall, configured to fulfill the role, or a dedicated server that interconnects all the participating users and systems. The upside of a dedicated server is usually easier scalability and overall higher performance.
Then there is the VPN client. In order to qualify for a VPN connection, the remote users and their devices need to be authenticated. This is particularly important when users are allowed to bring in their own devices (BYOD). There are several ways to do this:
- Digital certificates – A trusted certificate that is installed on the user device and verified when connection is established.
- Passwords – A pre-agreed password or a one-time generated password that the user has to enter before being able to connect.
- Client app – A special client app running on the user device that validates user credentials and their devices. This app can be proprietary or built-in as part of your OS.
Generally, the advantage of the client app is that it does not need any prior configuration by an IT administrator (this is not true for every vendor, but most follow this trend), enables easier internal management, and makes the VPN easier to use as well.
The client app also authenticates the user and establishes a secure connection with the VPN gateway. Once the connection is established, the remote worker has access to company systems and data as if they were sitting in the office.
What are the benefits of using a remote access VPN?
VPN solutions for remote access increase security and improve the productivity of remote employees.
Security is improved by the encapsulation of data in an encrypted tunnel, which protects it from interception. This is particularly important for remote workers who often connect via unsecured infrastructures, such as public wifi in a hotel, airport, or at home.
Especially when coupled with a static IP address, only traffic from the VPN gateway can be allowed to the systems (IP whitelisting), effectively creating a private LAN where only authorized users can connect and are cloaked from the public internet.
Productivity comes with the ability to connect to remote systems directly. This ability extends to devices of their choice, which means users can work from a comfortable environment that they create themselves.
Are remote access VPNs obsolete?
Yes. Remote access VPNs need to evolve if they wish to compete.
A remote access VPN in the traditional sense can no longer be a just fix to allow remote access to a perimeter-protected local network because this model itself is sinking into obsolescence.
Other models like zero trust network access (ZTNA), software-defined perimeter (SDP), or SSE (formerly SASE) are better suited for the displaced nature of today’s networks, where a remote access VPN can function as one of their components.
What are the alternatives to a remote access VPN?
Remote desktop software
The first alternative is a remote desktop application, which allows you to remotely connect to an endpoint on a local network via the internet. However, this solution is much less secure than a VPN as it does not encrypt data being sent between the remote user and the company endpoint.
Additionally, remote desktop applications are often less user-friendly than a VPN client. Some web-based applications are easier to use but they send data in clear text, which can be intercepted by third-parties, which means the security value of this remote access technique is null.
Digital workspace
Digital workspaces are seeing rapid adoption by enterprises thanks to their ability to centralize the management of remote access to applications. They are device-agnostic and improve user experience significantly.
On the other hand, you are limited by the number of tools supported by the workspace provider and, in some cases, are forced to only use the vendor’s own applications.
Security-wise, digital workspaces lack the network-layer encryption a VPN provides, and generally do not offer very robust access-control mechanisms.
ZTNA
Zero trust network access (ZTNA) is an emerging approach to network security that emphasizes encryption, strong authentication, network segmentation, and monitoring.
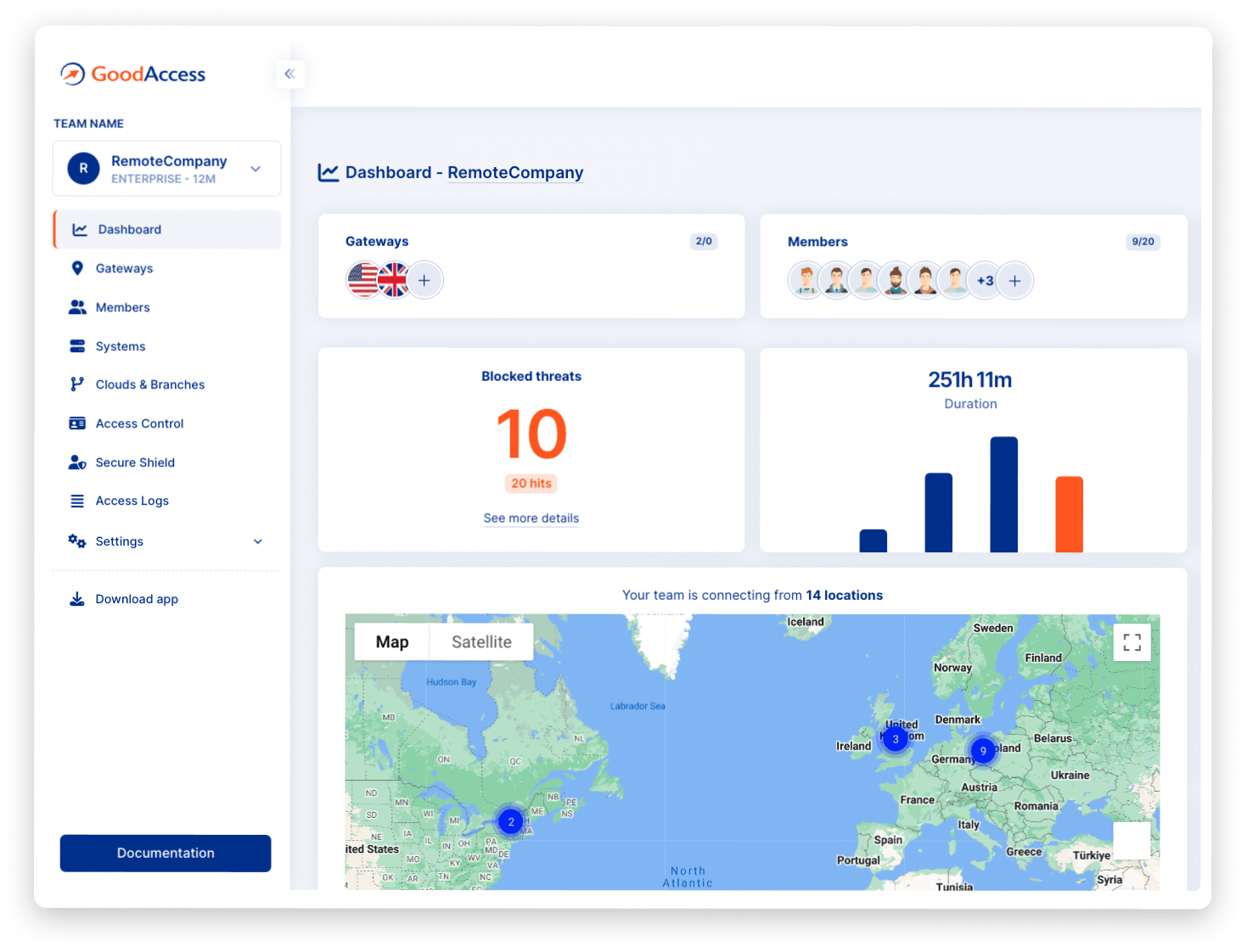
The encryption part is handled by a VPN technology in some ZTNA solutions (such as GoodAccess), with additional security layers built-in. ZTNA solutions with a VPN pedigree are very well suited for implementing zero trust in the context of remote access because from the start they are built with strong encryption in mind.
The above-mentioned security layers may include online threat detection and mitigation, two-factor authentication (2FA), robust access control, and even site-to-site VPN functionality and high-availability configuration.
Summary
VPNs for remote access serve an invaluable role in company remote access strategies, but, in their legacy incarnation, they begin to lag behind competitive solutions.
However, they still remain cost-effective solutions for small-scale use cases and often sit at the heart of more advanced models, such as ZTNA, where they provide remote-access functionality.