As companies embrace the hybrid way of working, they take different approaches to provisioning secure remote access. Some stick with a VPN (virtual private network) for remote access, while others adopt ZTNA (zero trust network access).
What are the advantages of ZTNA over VPN? And vice versa? This article compares the two solutions side by side and gives some recommendations for businesses.
Table of contents
What are ZTNA and VPN?
Feature comparison: ZTNA vs VPN
Architectural comparison
Regulatory compliance
Impact on business operation
Which is best?
What are ZTNA and VPN?
Both VPN and ZTNA deal with remote access, but they approach the task differently.
What is a VPN?
A virtual private network (VPN) is a traditional solution for securing remote access to network and internet resources. These include applications, data repositories, servers, or routers.
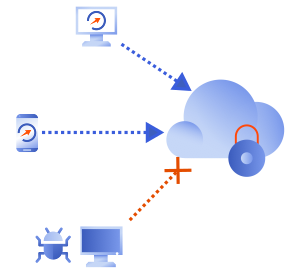
VPNs work by establishing a secure encrypted tunnel between the user and the remote endpoint/server/LAN.
Traditional VPNs do not limit application access, which means a connected user has free access to the network as if they were physically connected to the company LAN.

Common use cases of VPNs are:
- Remote access: Employees can access their company’s internal network remotely by logging in to a virtual private network.
- Improved security: VPNs provide an extra layer of encryption and authentication, making it more difficult for hackers to intercept sensitive data sent over the internet.
- Improved privacy: VPNs encrypt data to ensure that no one can track your online activities, which is especially important when using public Wi-Fi.
What is ZTNA?
Zero-trust network access (ZTNA) is a network security approach that relies on granular access to business applications. It uses secure authentication methods to verify the user’s identity and relies on robust access controls to limit access privileges to the necessary minimum.
ZTNA does not apply implicit trust. Instead, a ZTNA solution makes the user prove they are who they claim to be using identity-based authentication, typically reinforced by multi-factor authentication (MFA), context-based risk assessment (e.g. user location, number of unsuccessful login attempts), and policy adherence (e.g. device security posture check).
Only after proving their identity will the user be granted access to the system.
Common use cases of ZTNA include:
- Secure access to SaaS apps: ZTNA solutions can be used to provide secure access to cloud applications such as SaaS, IaaS, and PaaS by authenticating users and controlling access based on user roles and privileges.
- Secure remote access: ZTNA solutions can provide secure remote access to company on-site systems.
- Secure access for mobile devices: ZTNA solutions embrace device variety more easily, allowing employees to work from a device of their choice.
Middle ground: Cloud VPN
It is worth mentioning that there exist SaaS-delivered cloud VPNs that provide the same functionality as traditional hardware VPNs, but don’t require any hardware or much configuration.
Cloud VPNs with zero-trust network access features, such as GoodAccess, represent a sort of evolutionary middle ground between legacy VPNs and ZTNA.
Feature comparison: ZTNA vs VPN
Security
Both VPN and ZTNA are highly secure solutions.
VPNs focus on providing secure remote access via an encrypted tunnel. Therefore they ensure excellent security of data during transit. Point-to-point VPN connections are also highly private and excel at obfuscating the identity of the communicating parties.
However, the VPN technology as such does not protect against compromised endpoints. If an attacker gains access to the VPN, they have free rein of the whole network. This is a common attack vector for ransomware.
ZTNA solutions may also create encrypted connections, but this is no rule. Their primary security focus lies in authentication.
ZTNA authenticates users based on identity and authorizes them on a least-privilege basis. Least-privilege means access is granted only to a selected pool of systems and in a capacity that is required to perform the user’s role, but no more.
The idea behind this mechanism is that if an adversary compromises a user’s device and manages to gain access into the company network, they would not have free rein of the whole network, but only to those few systems that the user did.
ZTNA solutions are also built with compliance enforcement in mind, which means they generally keep access logs for monitoring and analysis.
Authentication vs authorization
User authentication is the process of identifying a user and verifying that they are who they claim to be. This is usually done through a username and password, but can also be done using biometric data or other methods.
User authorization is the process of determining what a user is allowed to do with a system. Authorization typically involves granting or denying access to certain areas or features of the system, or granting certain levels of privileges.
Flexibility
ZTNA offers more flexibility than a traditional VPN. ZTNA solutions are cloud-based, which means they can be implemented almost anywhere with little impact on user experience.
Traditional VPNs require more manual configuration and offer less flexibility. However, cloud VPNs provide an equal level of flexibility as ZTNA, albeit with a limited featureset.
Scalability
A traditional VPN is limited by the capacity of its VPN concentrator. Once you hit a performance ceiling, you need to deploy additional devices.
Cloud-delivered solutions like ZTNA or cloud VPN scale much better and don’t require any additional devices to do so. The ability to add users and systems easily to the protected environment is a core functionality of ZTNA solutions.
Reliability
Generally, hardware VPNs tend to be highly reliable due to their relatively simple architecture. However, this only applies as long as the VPN is properly and regularly maintained.
The SaaS-delivered ZTNA has to negotiate more potential points of failure along the way, but despite this, cloud-delivered solutions are usually as reliable as hardware infrastructure. This is because service providers are highly motivated to ensure service availability and will therefore conduct regular maintenance, keep their infrastructure up to date, and deploy high-availability configurations.
Management complexity
ZTNA generally provides a superior user experience to a legacy VPN. This is because traditional VPNs require complex configuration by a trained IT admin.
Cloud-delivered ZTNA, on the other hand, requires no hardware and minimal installation. The management overhead rests entirely with the provider.
Cost
Hardware VPNs require significant initial investment in hardware and associated maintenance costs down the line.
SaaS solutions, like ZTNA, require no hardware investment or maintenance costs whatsoever. You just pay the monthly/annual service fee plus additional services.
However, it is worth noting that really high-end ZTNA features, such as network anomaly detection, will come with a hefty price tag, often beyond the budget of small businesses.
Architectural comparison
The original purpose of VPNs was to serve as a “safe door” through a company perimeter to allow remote access. On the other hand, ZTNA is designed to be perimeterless from the ground up.
Zero trust network access (ZTNA):
- Disregards implicit trust, always verifies
- Uses micro-segmentation to portion the network to smaller sections
- Uses identity and context-based access control
- Uses encryption to protect data during transit
- Uses application-level firewalls to control access
Virtual private network (VPN):
- Uses encryption to protect data during transit
- Uses tunneling protocols to establish secure connections
- Uses a single point of authentication to verify identity
- Uses a centralized gateway to connect to the secured private network
- Uses a single set of access rules
Regulatory compliance
ZTNA and VPN show different levels of regulatory compliance readiness.
ZTNA offers a very granular approach to compliance, which allows companies to manage access per application. VPNs are more general in this regard, traditionally granting access to the entire network.
In addition, ZTNA solutions are compliance-ready, keeping access logs and providing visibility into user activity and barring access on the resource level. VPNs typically lack this capability and only grant access on the network level.
Impact on business operation
The choice between ZTNA and VPN impacts not just on company security, but also employee productivity and mobility.
Productivity
ZTNA offers flexibility in user authentication, which makes it easier to manage access to application data.
The flexibility of ZTNA also allows for easy secure access for contractors and customers. This makes sharing assets between both parties much easier and gives an overall boost to collaboration.
Mobility
ZTNA also has an edge over VPN in terms of mobility. Since it doesn’t require any (or only minimal) installation, users can use whichever devices they choose. This is in sharp contrast to the configuration of VPN clients on legacy VPNs.
Which is best?
The differences between a VPN and ZTNA stem from their different histories and goals. VPN provides direct tunneled access to a LAN or server, while ZTNA provides access to explicitly authorized applications and services for remote users.
So, should you use ZTNA or VPN?
- Small companies that only have a few remote employees are better off with a modern, cloud VPN. A VPN provides secure and private connections on unsecured networks (e.g. public Wi-Fi) while the employees connect remotely. A cloud VPN is the best solution for companies that don’t have trained IT admins on staff.
- ZTNA is best for companies with a large number of remote workers. Once set up, it provides better user experience, fits well with a corporate ecosystem of SaaS apps, and scales more easily.
| ZTNA | Hardware VPN | Cloud VPN | |
|---|---|---|---|
| Cost | Moderate on a small scale, higher in large deployments | Initially high | Low |
| Management complexity | Low | High | Low |
| Scalability | High | Low | High |
| Reliability | High | Very high | High |
| Feature set | Rich | Moderate | Moderate |
| Security | Very high | High | High |
Tab. 1 – Comparison of ZTNA, hardware VPN, and cloud VPN
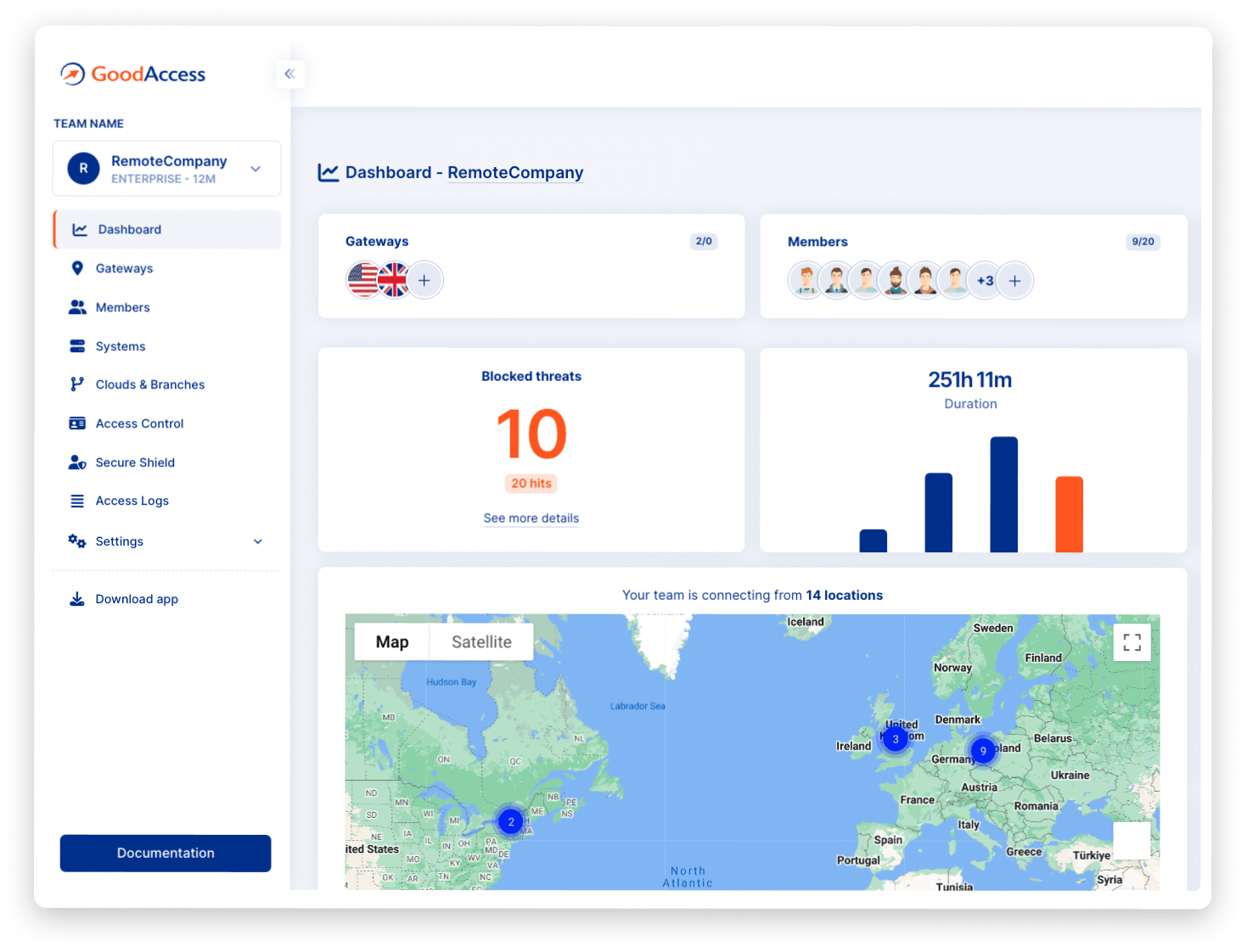
Mature SaaS security solutions, like GoodAccess, tick the boxes of both cloud VPN and ZTNA. The GoodAccess Essential plan provisions a cloud VPN for small and medium businesses, while the Advanced plan offers robust access control and secure branch/cloud connectivity for companies seeking to deploy full-fledged ZTNA.
Try it out for free for two weeks here.