Ports are the gateways for data communication used by apps and services. Understanding reconnaissance sweeps of a company system’s ports is crucial to keeping it safe—whether to detect potential intruders or to check the strength of your own defenses.
This article explains what port scanning is, what techniques there are, and how to defend against port scanning attacks.
Table of contents
What is port scanning?
What is a port scanner?
What port scanning techniques are there?
What is a port scanning attack?
How do you prevent a port scanning attack?
What is port scanning?
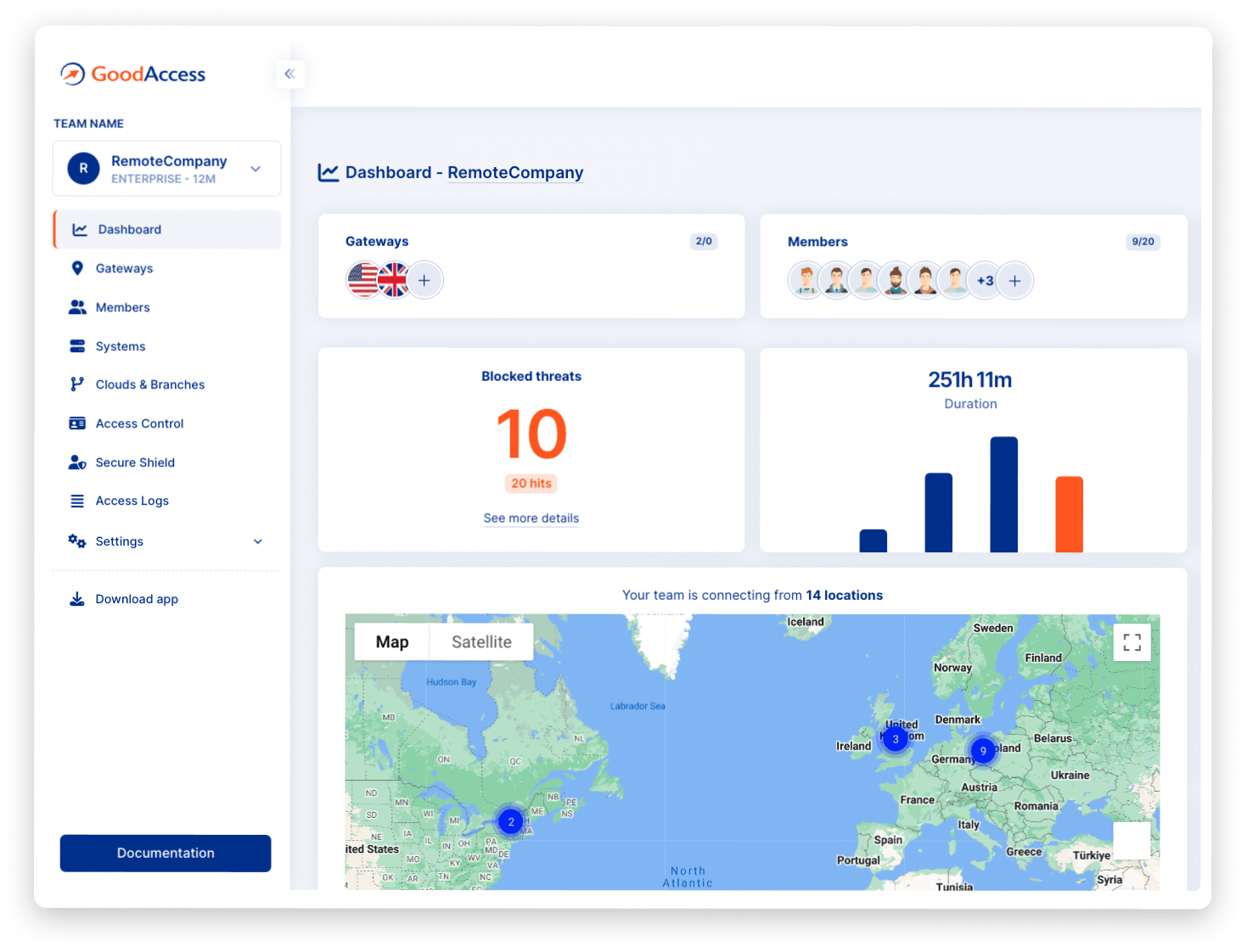
Port scanning is a networking technique that determines what ports on a network device are open and can receive or send data.
Network and security administrators use port scanning to discover potential vulnerabilities in their network—an open port represents a potential point of entry for an attacker.
It also tests for the presence and strength security measures, such as firewalls, that lie between the internal systems and the public internet.
Hence, this same technique is also used by cybercriminals for network reconnaissance and identification of potential targets.
What is a port?
A port (or port number) is a numerical identifier of an endpoint or service taking part in a connection. For example the most common transport protocols, like TCP and UDP use port numbers.
A port number forms a tandem with the host’s IP address, and together they identify the connection, so that data is successfully routed from the sender to the recipient.
Port numbers range from 0 to 65535, with numbers 0 to 1023 being the most common ports used by network and application services.
Certain port numbers are reserved for specific services as a general standard. Clients then know which is the “default” port for these services.
Here are a few examples of port numbers of well-known services:
- FTP = 20, 21
- SSH = 22
- SMTP = 25
- HTTP = 80
- HTTPS = 443
Network administrators, penetration testers, and cybercriminals use tools called port scanners to perform network scans.
What is a port scanner?
A port scanner (port checker) is a piece of software that network admins use to identify open ports on a device or network.
Port scanners send requests to ports on the target system and listen for the response. Based on this, the port scanner determines whether the port is open (listening and responsive), closed (not listening and unresponsive), or filtered (blocked by a firewall).
This information helps network and security admins to check the security posture of their network, but attackers can use these tools as well. Often, the response of the service listening on a particular port tells the port scanner what software is using that port, sometimes even the version, based on which they can look up an exploit to hijack the service.
What port scanning techniques are there?
There are several types of port scanning techniques. Below is a list of the most common ones:
- Full connect scan (vanilla)—In a full connect scan, the port scanner sends a request for a full TCP connection to the target, which goes as follows. It sends a request to connect (SYN flag), waits for an acknowledgement of connection (SYN-ACK), and confirms by sending back an acknowledgement (ACK flag). This exchange is called the TCP handshake. Once the connection is established, the port scanner drops the connection. This method is accurate but slow. Firewalls usually log this exchange, so it is also easy to detect.
- Half-open scan (TCP SYN scan)—A half-open scan also sends out a connection request (SYN) but only waits to receive the SYN-ACK response. This is enough to know the port is open, but because the connection is never actually established, the system does not log it.
- TCP ACK scan—This type of scan focuses on firewall rules by determining whether a port is filtered or not (it cannot tell if a port is closed or open). A TCP ACK scan sends a packet that only has the ACK flag. If the target responds with an RST packet, it means the port is unfiltered.
- XMAS scan—In an XMAS scan, the port scanner sends packets with invalid flags, e.g. FIN, which indicates a session termination. If the target makes no response, the port is considered open. If it does respond, it is closed. XMAS scans are less commonly picked up by firewalls.
- UDP scan—In a UDP scan the scanner sends a UDP packet at target. If it receives a UDP packet in response, the port is open. If not, the port is either closed or filtered, depending on the error code.
- FTP bounce scan—The port scanner bounces the packet via a proxy FTP server. This helps disguise the sender’s location and could also help bypass the firewall.
What is a port scanning attack?
As mentioned earlier, cyberattackers perform port scanning attacks to identify weak points they can exploit as points of entry.
Port scanning attacks occur early into a cyberattack, during the reconnaissance stage.
Typically, the attacker will perform a network scan to get a list of active devices on the network and then scan their ports to find out more about them, such as what devices are online, what applications are running, and what defenses there are.
This information is of value to the cyberattacker when deciding the next approach; that means what systems present an opportunity for infiltration, how they are protected, and what vulnerabilities they might have.
How do you prevent a port scanning attack?
While not dangerous on their own, port scans nevertheless betray dangerous activity that can lead to dreadful consequences. There are several techniques that organizations can use to prevent cyberattackers retrieving the information they want.
- Firewall—Firewalls provide visibility and control over ports on your network, and can detect some attacks and automatically block them.
- Intrusion prevention system (IPS)—Intrusion prevention systems monitor network traffic and automatically block detected threats.
- Anomaly detection—Anomaly detection systems pick out unusual traffic patterns, such as port scans, and, while they don’t usually block the malicious traffic themselves, they notify the admin and often pair with a firewall for automated blocking.
- Keeping your ports closed—Less of a countermeasure and more of a best practice; always make sure you don’t keep any unnecessary ports open, and use techniques like port forwarding only when you know what you are doing.