GoodAccess is entering a whole new tier among ZTNA offerings.
Meet System-Level Access Logs, a game-changing enhancement to your IT environment’s observability.
At a glance:
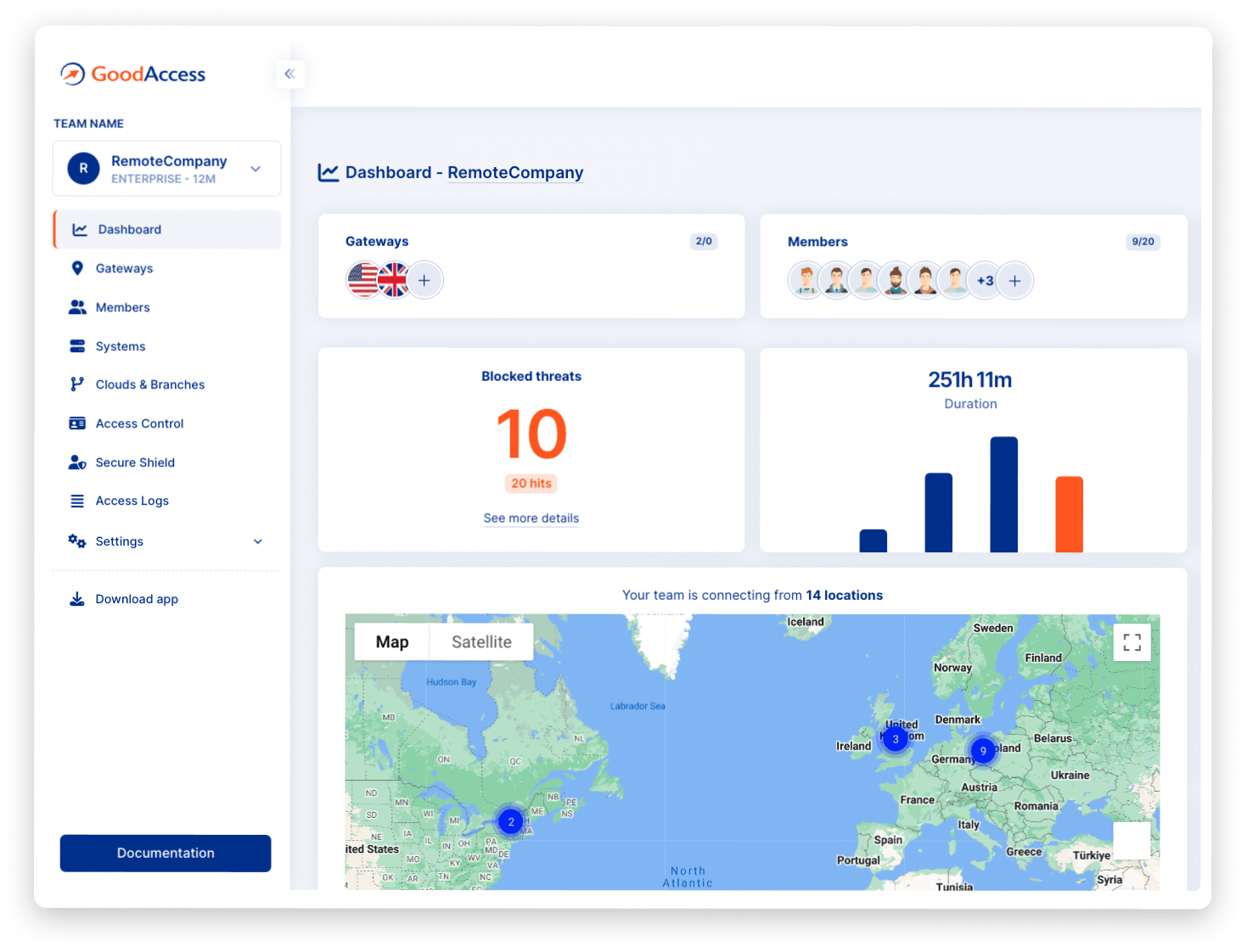
- System-level access logs allow you to monitor user-application interactions.
- They provide granular information on user devices and other interaction data.
Track activity on each system
System-level access logs allow you to see who interacted with which system, how long the session was, and how much data was transferred.
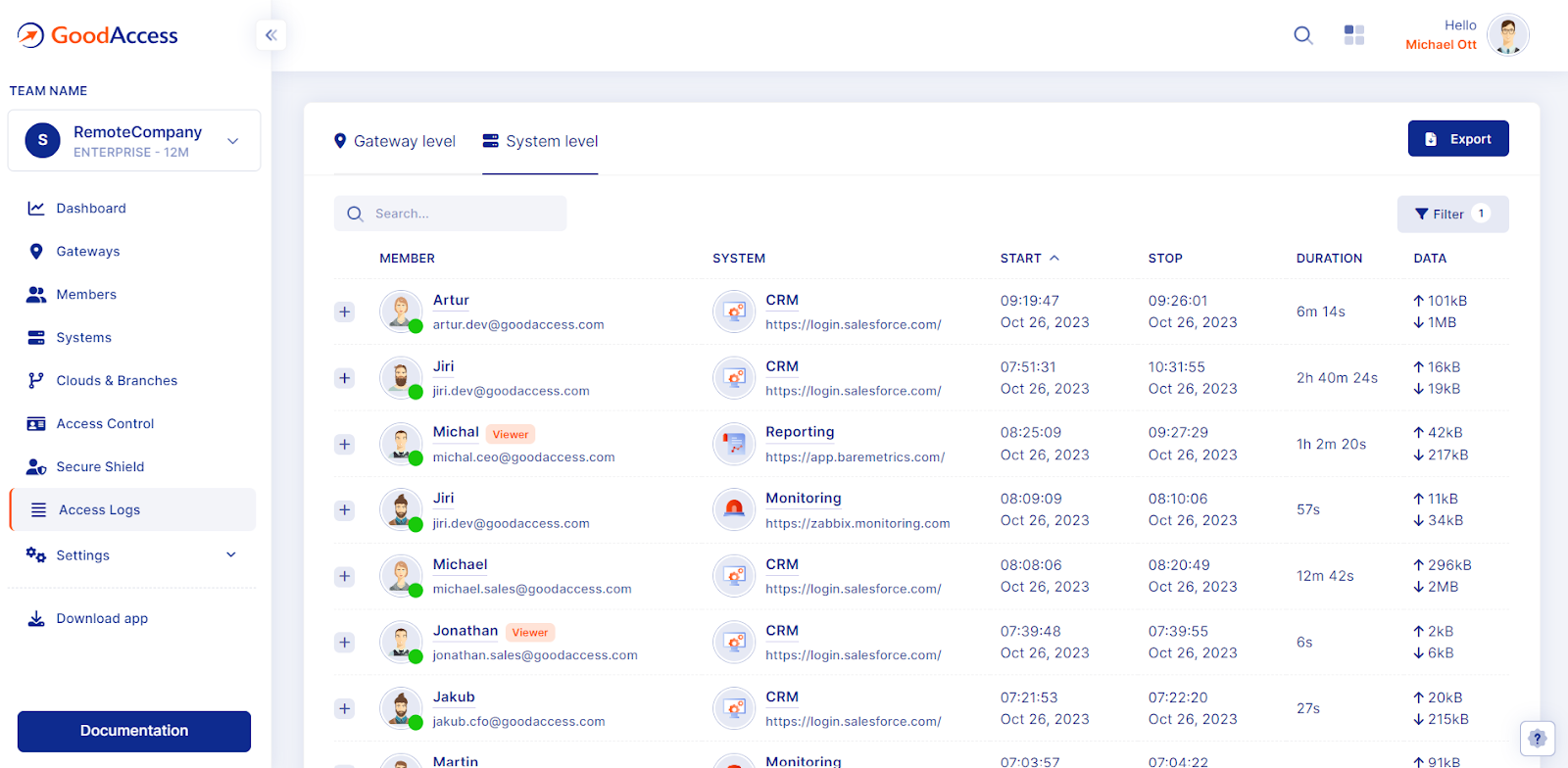
You can filter the session records (e.g. to view the activity on a particular application) and export the records for later analysis.
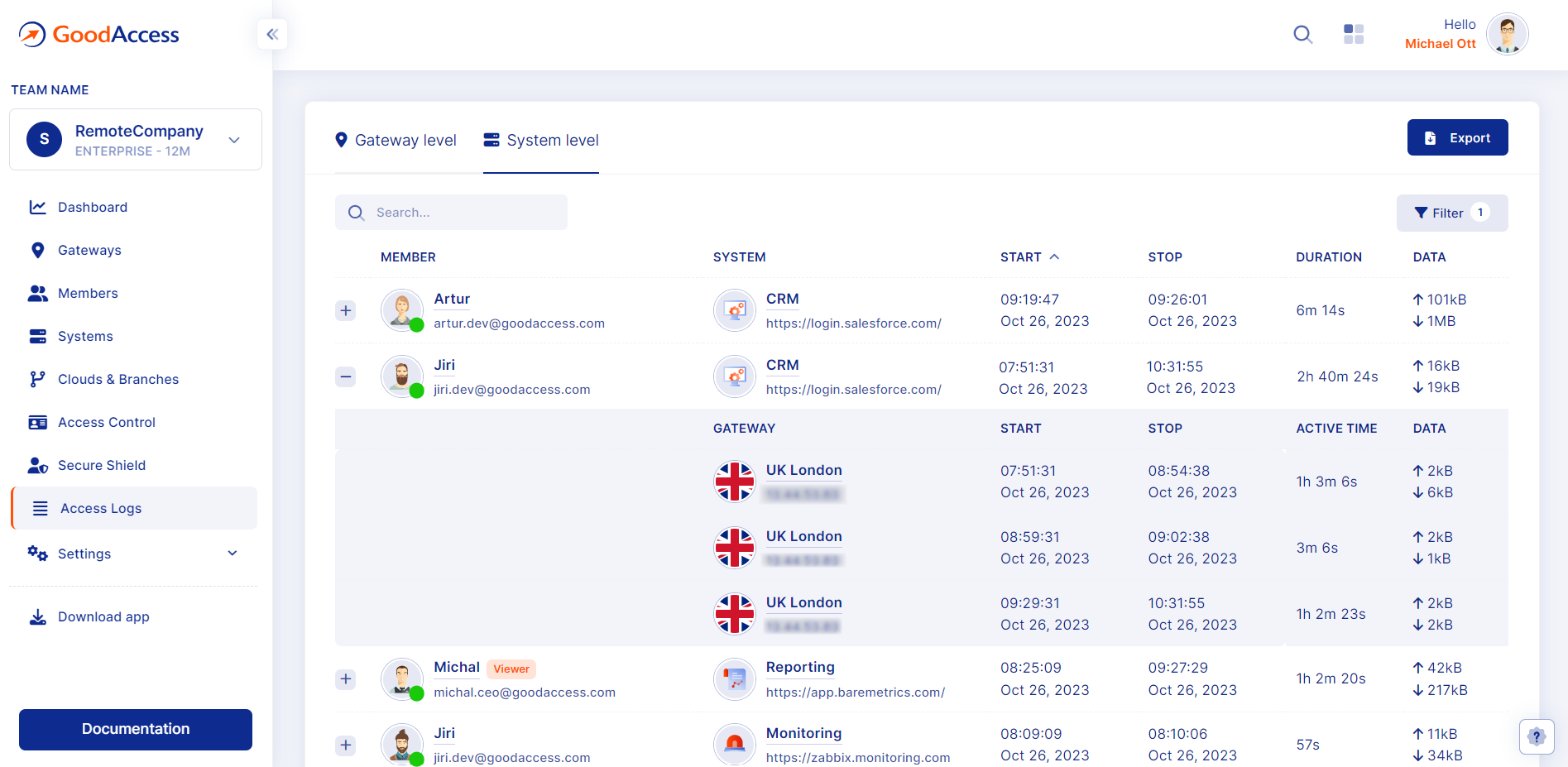
Drill down to details
By expanding a session record you can investigate individual user-application interactions. This provides additional detail, such as more granular interaction timestamps or the device and gateway that was used for the connection.
System-level access logs vs gateway-level access logs
Gateway-Level Access Logs provide a quick glance of who has connected to your software-defined perimeter.
System-Level Access Logs give you much more granular information on interactions with individual systems. This makes them a much richer source of intelligence for monitoring or incident investigation.
Closing remarks
System-Level Access Logs can be found in the Control Panel in the Access Logs section and under the System Level Tab. They come with the Premium plan.
System-Level Access Logs are an essential component of activity monitoring, which is a necessary part of compliance with NIS2 and other data protection regulations.
Do you have any feedback? Let us know!