The NIS2 Directive heralds major changes for many organizations across Europe, prompting changes in national legislation that mandate a broader scope of cybersecurity measures, including zero trust as an essential risk-management mechanism.
Table of contents
Glimpse back to the history of NIS
What is NIS2
The goal and main objectives of NIS2
Who does NIS2 apply to?
Zero-trust and NIS2 compliance readiness
Understanding zero trust
The benefits of zero trust
Wrapping up on zero trust and NIS2 compliance
How GoodAccess can help you with NIS2 compliance
FAQ
The past decade established information systems as integral parts of the everyday lives of individuals, businesses, and states all over the world, while the covid-19 pandemic only accelerated this digital transformation.
Besides the indisputable benefits that technology brings, the rapid digitalization also fueled an expansion of the threat landscape. Incidents have increased in volume, frequency, sophistication, and impact, and security authorities predict the trend will only grow. Just consider the following statistics
- The cost of cybercrime more than doubled in two years (from 2.95 trillion USD in 2020 to 7.98 trillion USD in 2022), Statista Technology Market Outlook
- The cybersecurity market has experienced rapid growth over the last few years with revenue increasing from US$115 billion in 2019 to US$147 billion in 2022. (Statista Technology Market Outlook)
- It takes an average of 277 days for security teams to identify and contain a data breach, according to "Cost of a Data Breach 2022," a report released by IBM and Ponemon Institute.
- The most common attack vector is stolen or compromised credentials, followed by phishing (IBM, Cost of a data breach 2022 report)
- European organizations allocate 41% less on cybersecurity than their US counterparts (ENISA, 2020)
Faced with the evolving cybersecurity threat landscape, the European Union decided to take coordinated steps towards “high common level of cybersecurity in the EU” and formulated them in the NIS2 Directive (The Network and Information Security).
Glimpse back to the origins of NIS
The EU's cyber law efforts date back to 2013 when the first cybersecurity strategy was created. It took three years to develop the first EU-wide legislation on cybersecurity - The Directive on Security of Network and Information Systems across the Union (the NIS Directive, 2016).
The NIS Directive aimed to achieve a high common level of cybersecurity across the Member States via introducing several requirements, emphasizing the most exposed entities from industries like transportation, energy, healthcare, water supply, etc. (known as critical infrastructure). Amongst many other things, NIS Directive also established the network of national CSIRT teams.
In 2020, two years after the member states had successfully transposed the NIS Directive to respective national legislations, ENISA conducted an extensive study and considered the Directive to had an overall positive effect, especially in terms of driving cybersecurity investments.
However, as stated by The Executive Director of the EU Agency for Cybersecurity, Juhan Lepassaargaps, “gaps still existed”, such as insufficient level of cyber resilience of businesses operating in the EU, difficult implementation, inconsistent resilience across member states and sectors, and lack of joint crisis response.
Facing the new, dramatically different reality than that of 2016, the EU decided to review the NIS directive and extend its scope in order to meet current risks and future challenges.
What is NIS2
The NIS2 Directive is an EU-wide cybersecurity legislation that aims to improve the overall cyber resilience across the member states and internal market.
The Directive formulates an institutional and regulatory approach that requires more public and private entities to implement modern security measures, reduces inconsistencies across the Union, and improves EU-wide cooperation on cybersecurity experience sharing and incident handling.
NIS2 (officially The Directive on measures for a high common level of cybersecurity across the Union) also introduces stricter supervision, enforcement measures, fines, and sanctions for not complying with the Directive.
It became effective 16 January 2023 and the Union's member states now have less than 2 years to transpose the Directive into their national legislation (by 17 October 2024).
NIS2 replaces the original directive from 2016, and as stated in the Briefing to the Directive, its objectives are to “strengthen the security requirements, address the security of supply chains, streamline reporting obligations, and introduce more stringent supervisory measures and stricter enforcement requirements, including harmonised sanctions across the EU.” (Briefing, The NIS2 Directive: A high common level of cybersecurity in the EU, 2023).
The goal and main objectives of NIS2
The goal of the NIS2 Directive is enhancing the cybersecurity of network and information systems across the EU. It represents a significant step towards strengthening cyber resilience in the EU, reflecting the evolving threat landscape and increasing importance of digital services for the functioning of society and internal market.

There is no doubt this is an ambitious target. Looking at the Directive, there are four main objectives that should lead to its successful fulfillment:
- Broader scope. NIS2 expands the scope to include more sectors and services as either essential or important organizations. To the original scope of 7 industries are added 8 new, including providers of public electronic communications networks and services, digital services (social networking services, data center service providers), waste management, and others. See this factsheet published by the Commision to learn more.
- Stricter requirements. NIS2 introduces more stringent security requirements, including supply chain security, business continuity, crisis management, cybersecurity training, access control policies, use of MFA or continuous authentication methods, and others. If you want to dig deeper into these requirements, check out our article where we break down 10 minimum cybersecurity risk management measures of NIS2 directive.
- EU-wide cooperation. The Directive sets the basics for establishing the European Cyber crises liaison organization network (EU-CyCLONe) that should be a central point for coordinated action against large-scale cybersecurity incidents and information/experience sharing.
- Enhanced supervision. There will be an enhanced supervision, incident reporting obligations, and fines for non-complying with the Directive. Management of the affected entities can now also be held directly accountable for legal infringements.
Who does NIS2 apply to?
NIS2 requires securing everything related to providing essential services that are necessary for the society and the functioning of the internal market.
The Directive lists 18 obligated sectors and classifies obligated entities into two categories: essential and important. This distinction is based on the extent of how critical they are for the particular sector as well as the type of the provided service.
NIS2 covers the following obligated sectors:
Energy, Transport, Banking, Financial market infrastructures, Health, Drinking water, Waste water, Digital infrastructure, ICT service management, Public administration, Space, Postal and courier services, Waste management, Manufacture, production and distribution of chemicals, Production, processing and distribution of food, Manufacturing, Digital providers, Research.
However, the fact that the public or private entity falls under the listed sectors does not imply their obligation by default. This obligation arises only if the organization meets the following two criteria:
- Importance: The entity provides services mentioned in at least 1 of the sectors listed in Annex 1 and 2 of the Directive.
- Size: Enterprises with more than 50 employees or more than 10 million euro revenue will be obligated to comply with NIS2.
However, there are exceptions and entities providing selected essential services will have to comply no matter their size (e.g. DNS service providers). See the General provisions of the Directive, (7), and Annex 1 and 2 for further guidance.
Zero-trust and NIS2 compliance readiness
The NIS2 Directive addresses the cybersecurity challenges by requiring essential and important entities to adopt several security measures listed in Article 21 of the Directive. Mandating zero-trust as a basic practice of cybersecurity hygiene is one of them.
“Essential and important entities should adopt a wide range of basic cyber hygiene practices, such as zero-trust principles, software updates, device configuration, network segmentation, identity and access management or user awareness”
Source: DIRECTIVE (EU) 2022/2555 OF THE EUROPEAN PARLIAMENT AND OF THE COUNCIL, (89)
What is zero trust
In network security, zero trust approach builds on the assumption, that all network traffic is potentially malicious (cannot be trusted). Therefore every user, device, and network connection must be verified and validated before granting access to digital resources. It improves the overall cybersecurity posture of the organization, reduces the risk of breaches, unauthorized access and lateral movement. To learn more about zero-trust, navigate to our dedicated ZTNA knowledge base.
Since the NIS2 directive implicitly promotes zero trust, it will play a key role in the efforts of organizations to meet regulatory compliance. Let's take a look at its principles and benefits.
Understanding zero trust
The term “zero trust” originates from the belief that no user, device or even a transaction should be inherently trusted. So, when embracing this approach to your organization's network, it is crucial to eliminate the implicit trust that users commonly enjoy in corporate LANs, and replace it with strict and continual verification.
But there is more than just leveling up your access management. Usually there are four basic principles of zero trust:
Identity-based user verification – Every user must prove the legitimacy of access before being admitted to an internal system. To approach this, zero trust organizations require multi-factor authentication, device check posture, biometrics and other authentication measures. All communications are encrypted.
Transaction verification – All connections should be verified and assessed before being established.
Least-privilege principle – Users only receive access privilege to those systems they need for work.
Continuous monitoring and threat detection – Suspicious behaviors need to be identified to weed out both known and zero-day threats.
The least privilege principle
The principle of least privilege means that users and devices are provided with the minimum necessary access required to perform their work. For example, a user from the marketing department might be assigned access rights to the CRM, but their access to e.g. financial system and managerial resources are denied by default. Learn more about the least privilege principle and other key elements of zero trust in our dedicated blog on zero trust authentication.
Practical implementation of zero trust typically involves a range of different security controls and processes. For example, multi-factor authentication, device posture check, network segmentation, access control, traffic monitoring, data protection, etc. All of these should work together to ensure that every transaction meets the required conditions.
As a result, building the zero-trust competencies from scratch in order to successfully comply with the NIS2 Directive might be a difficult and resource-intensive process. This is why vendors such as GoodAccess deliver cloud-based zero-trust solutions that cover everything needed.
How does zero trust access work in practice
For example, if a user wants to access a sensitive file from a mobile device, the request will be verified by checking the user's identity, the device's security posture, and the context of the request. By applying the least privilege principle, the user is granted access only to the resources they are allowed to. If any of these conditions are not met, the request will be denied, and access will not be granted.
The benefits of zero trust
Zero trust provides a more secure but also more flexible environment for organizations, particularly as they increasingly rely on cloud, remote workforce and mobile technologies.
It is a successor to traditional perimeter-based security which proved obsolete in the world of ever-changing threats, omnipresent mobility, and distributed IT resources.

The benefits of zero trust architecture include:
- Enhanced security – Zero trust security approaches help to prevent unauthorized access and protect against external and internal threats, boosting the organization’s cybersecurity capabilities.
- Improved visibility – Zero trust security solutions provide observability into user and device access across the given environment. This helps to identify suspicious activity and potential threats in real-time.
- Reduced risk – By implementing a zero trust security model, organizations can reduce the risk of damage caused by data breaches, lateral movement and other cyberattacks.
- Increased efficiency – Zero trust security solutions can help streamline authentication and authorization processes, which can result in improved efficiency and productivity.
- Improved compliance – Zero trust security solutions can help organizations meet compliance requirements such as NIS2 by providing comprehensive security monitoring and incident reporting to competent authorities.
Wrapping up on zero trust and NIS2 compliance
The recently adopted NIS2 Directive requires entities to adopt several new cybersecurity measures. The goal is to increase preparedness and effectiveness in order to mitigate risks caused by rising digitalization.
Even though we do not know how exactly the Directive will be transposed to national legislation, compliance with NIS2 will become an everyday reality for many companies.
Since NIS2 explicitly mentions zero trust as a readiness approach for the compliance efforts, zero trust is no longer nice-to-have, it becomes almost a legal requirement. But it doesn't have to be a tough job to implement zero trust into your organization.
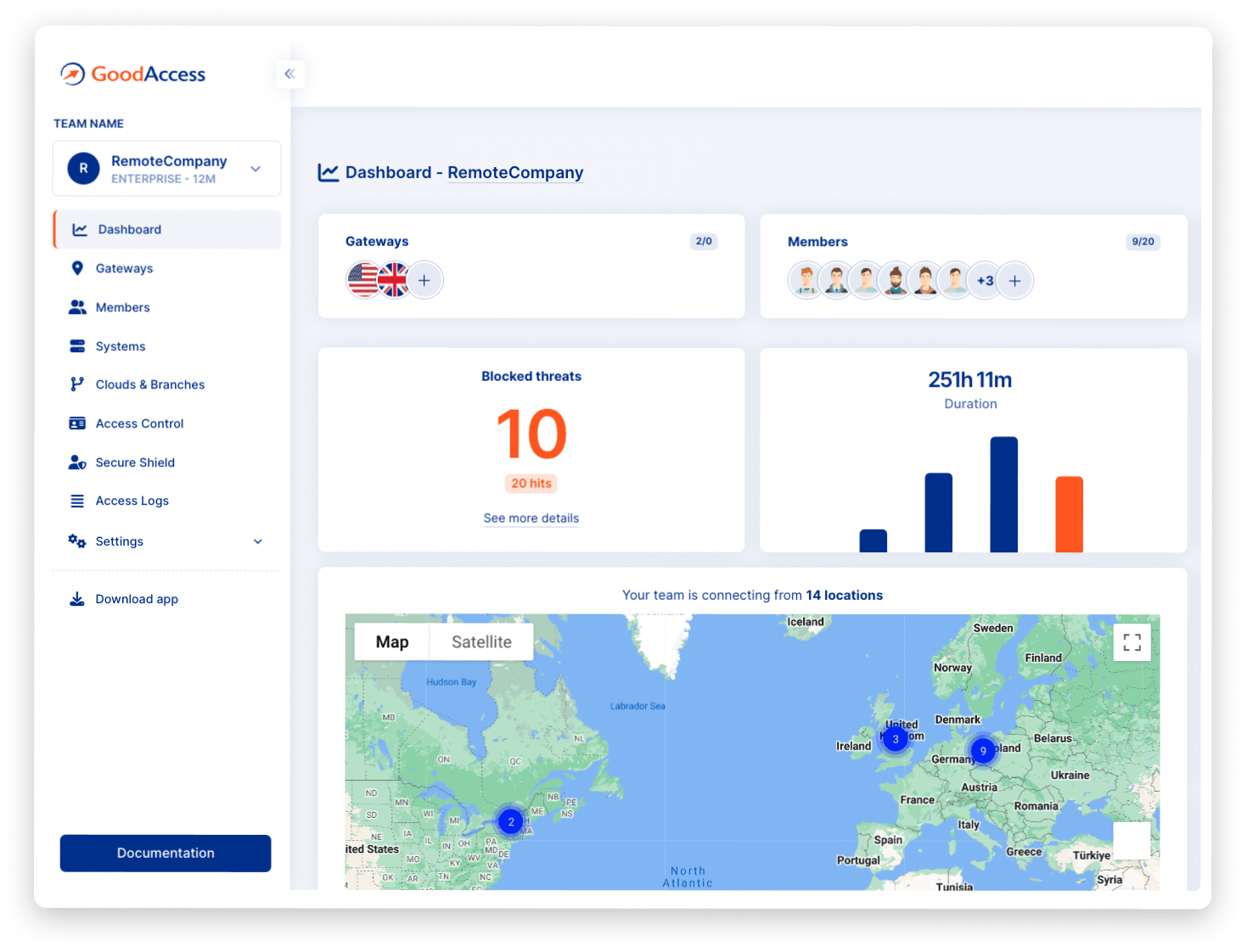
GoodAccess and NIS2 compliance
GoodAccess is a proven zero trust network access solution that helps businesses to comply with the technical requirements of NIS2. It helps to protect network and information systems by delivering security measures proposed in NIS2, such as:
- Incident detection—network-based online threat detection and system-monitoring.
- Encryption—in-transit encryption shielding data from interception and eavesdropping.
- Identity-based access management—least-privilege access control on the network level, which adds a security control over any resource (old or new) in your IT infrastructure.
- Multi-factor authentication—network-based MFA that prevents unauthorized access and credential misuse
All of this in one suitable SaaS solution, that is easy to use and deploy.
Follow this link to learn more about achieving NIS2 compliance with GoodAccess or contact our team to learn more.
If you want to learn more about zero trust network access, its key principles and deployment, read this dedicated blog.
FAQ
What is the NIS 2 Directive for cybersecurity?
The NIS2 Directive is a legislation that aims to improve the overall cybersecurity resilience of the EU, the member states and internal market. Essential and important entities from 18 sectors defined by the Directive, such as banking, finance, healthcare, transportation and others, are required to take appropriate technical, operational and organizational measures to manage the risks posed to the security of network and information systems. These measures include policies on risk analysis and information system security, protection of supply chains, encryption, access control and others (see article 21 of the Directive).
What is the difference between NIS and NIS 2?
The main differences between NIS and its successor NIS2 lie in broader scope, stricter requirements, enhanced supervision and the aim to elevate EU-wide cooperation by establishing the European Cyber crises liaison organization network (EU-CyCLONe).
What is the purpose of the NIS2?
The main purpose of the NIS2 Directive is enhancing the cybersecurity of network and information systems across the EU. It represents a significant step towards strengthening cybersecurity and resilience in the EU, reflecting the evolving threat landscape and increasing importance of digital services for the functioning of society and internal market.
What sectors are covered by NIS2?
The NIS2 Directive covers the following sectors: Energy, Transport, Banking, Financial market infrastructures, Health, Drinking water, Waste water, Digital infrastructure, ICT service management, Public administration, Space, Postal and courier services, Waste management, Manufacture, production and distribution of chemicals, Production, processing and distribution of food, Manufacturing, Digital providers, Research.
What does NIS2 mean?
The abbreviation NIS refers to “The Network and Information Security”, the EU-wide cybersecurity law first introduced in 2016. NIS2 is a successor of the original NIS Directive which became effective in January 2023. The term “NIS2” is used to refer to the EU legislation which is officially named “Directive (EU) 2022/2555 of the European Parliament and of the Council on measures for a high common level of cybersecurity across the Union.
What are NIS2 requirements?
The NIS 2 Directive sets out various requirements for the EU member states, and consequently on essential and important entities from several sectors. The scope of the NIS2 Directive is quite broad and besides other things, it requires the obligated entities to adopt several security and cybersecurity risk management measures, develop incident response and reporting capabilities, and also requires creating an EU-wide cooperation network to cope with large-scale cyberattacks and for experience sharing.
Is NIS2 approved?
Yes, it is. The Parliament and the Council of the European Union reached a political agreement in November 2022. The Directive was then officially published by the Official Journal of the European Union on December 14th, 2022, and entered into force on January 16th, 2023. The member states of the EU now have less than 2 years to transpose the Directive into their national legislation (by October 17th, 2024).
What is the status of the NIS2 Directive?
The NIS2 Directive has become effective since January 16th, 2023. The EU member states now work on transposing the Directive into their national legislation which should be done by 17 October 2024.