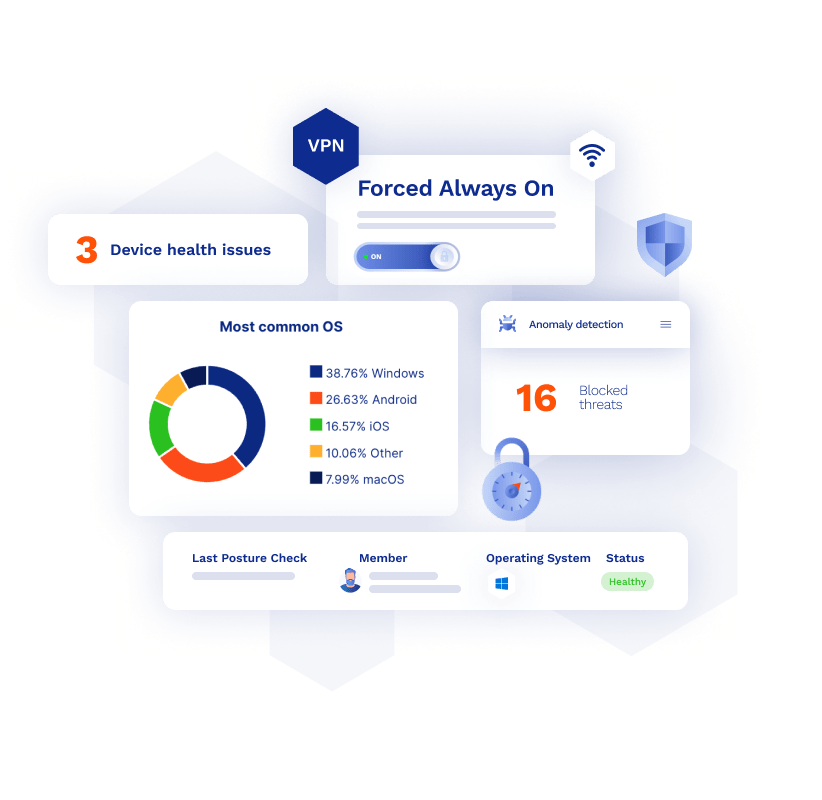
GoodAccess now has the ability to perform device posture checks and enable forced always-on connections.
These features will help you enable advanced rules for access to your secure IT environment and enforce them periodically.
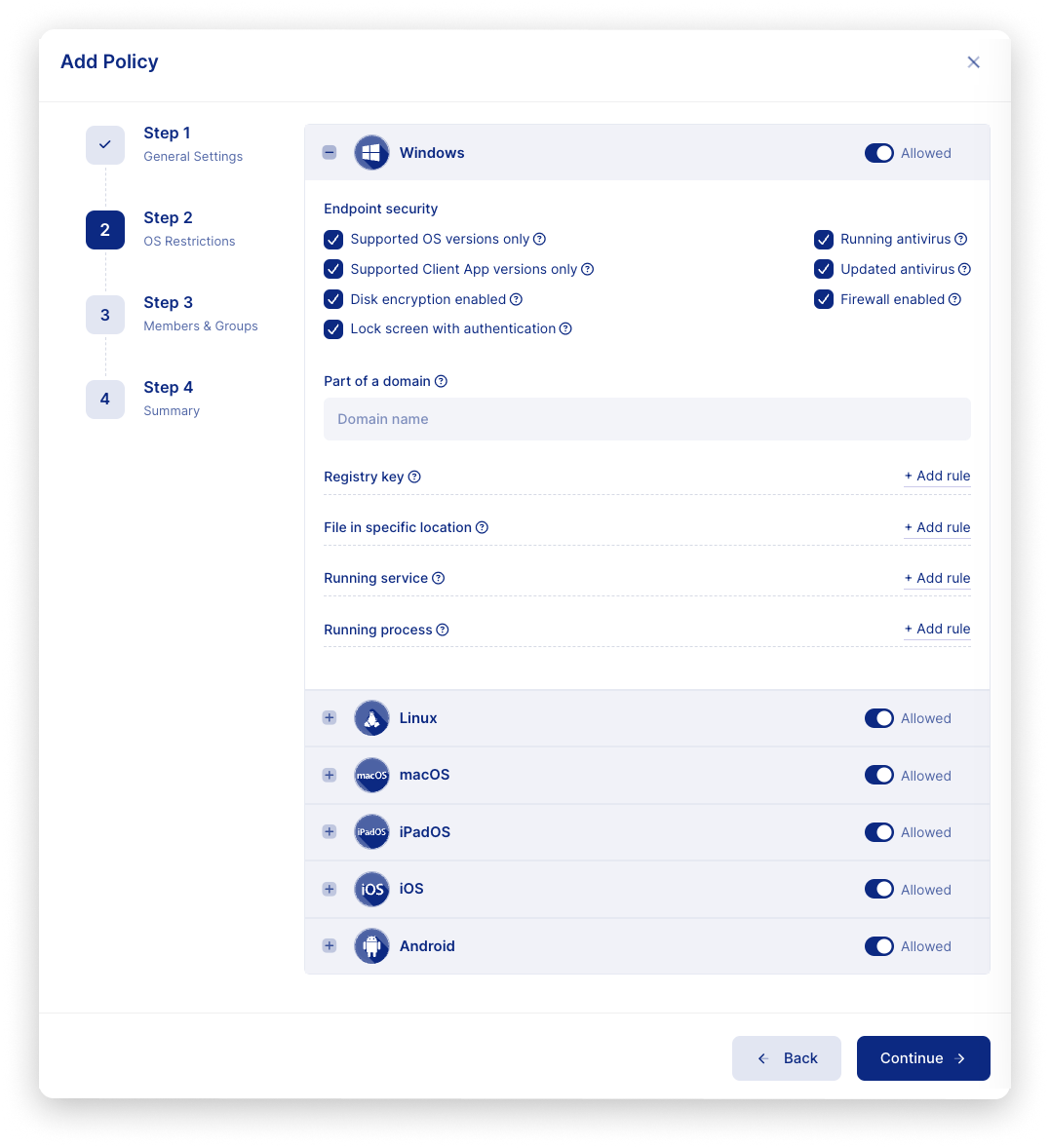
Device posture check
Device posture check is a security mechanism that prevents potentially risky user devices from connecting to or remaining in your secure IT environment.
GoodAccess checks the devices against a set of criteria that you can specify. Non-compliant devices will be recorded and (optionally) blocked from access until the issue is resolved and the device meets the criteria.
Here are a few examples of restrictions that you can set up:
- The device must have an active and up-to-date antivirus software
- The device must have a firewall on
- The device must have a lock screen enabled
- The device must have a specified domain
- The device must use a specified OS and version of OS
- The device must have a specified certificate installed
- The device has a specified value in the registry
These (and other) criteria allow you to permit only those devices that meet your security policy; i.e. they are secured, up-to-date, issued by your company—whatever criteria you define.
Why device posture check
Device posture check is similar to airport security screening.
Before you board an airplane, airport staff will check you and your luggage for potentially dangerous objects and substances—weapons, flammables, explosives, drugs. Specific things that they know to look for. If one is found, you have to get rid of it, or be denied entry to the craft.
Without a device posture check, your users can enter your secured perimeter with whatever device they wish. You have no control over such devices and have no way of knowing whether they don’t pose a potential threat.
Device posture check ensures that only compliant devices can be within your perimeter. This is both good security practice and an essential part of regulatory compliance for device security and remote access.
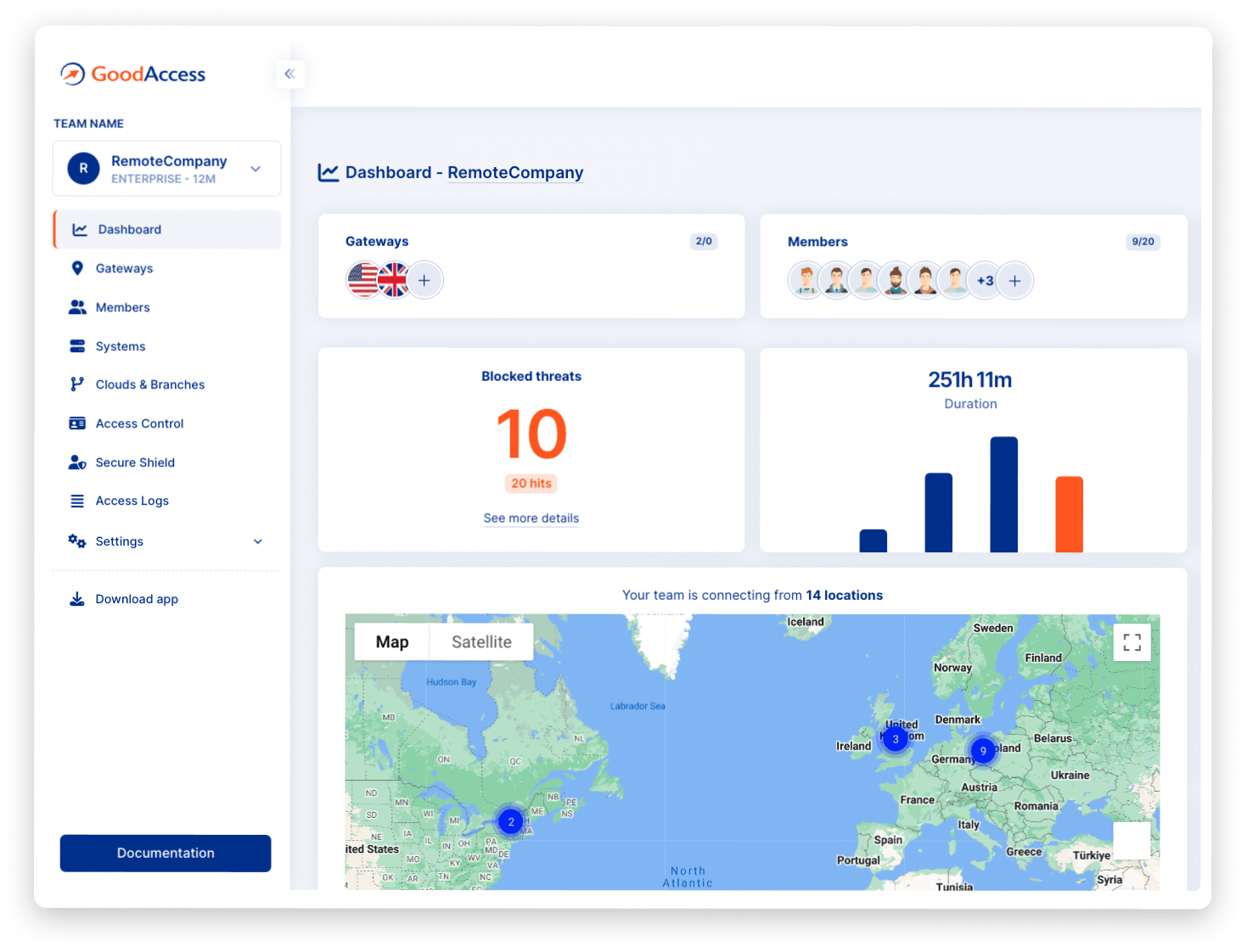
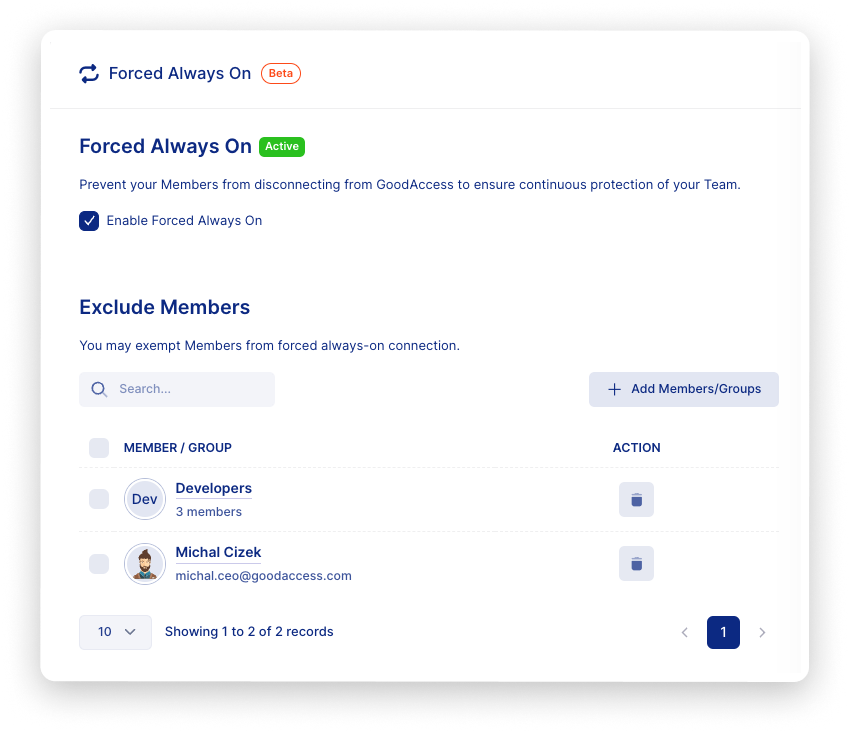
Forced always-on connection
An always-on VPN connection remains active as long as the user’s device is powered on.
GoodAccess’ forced always-on connection is centrally controlled by the admin and prevents the user from accessing critical systems without proper authentication and security measures (e.g. network encryption and threat detection).
When a user attempts to disconnect, they receive an error message telling them that disconnecting has been disabled.
In special cases, you may manually exempt selected users from forced always-on.
Why forced always-on
Forced always-on connection ensures that users always have appropriate security measures enabled.
This gives you peace of mind that security policies are maintained and users are protected regardless of their location. This protection encompasses in-transit data encryption, online threat protection, least-privilege access control, and content policy enforcement.
This is particularly useful in remote-access scenarios when users use untrusted Wi-Fi networks to connect.
No gambling on company laptops
Your company wants employees to connect only via company-issued devices and wants to ban gambling during work.
In GoodAccess, this is easily done.
You set up device posture check to your company’s domain name to only allow company devices in.
Then you activate forced always-on to ensure the users cannot disconnect from GoodAccess, and block known gambling sites in Custom Domain Blocking.
Now, you have the certainty your users are always protected on untrusted (or any) networks, and your security and content policy is enforced throughout.
Summary
Advanced, continual access controls are a necessary component of any security policy of today’s digital companies, and one of the pillars of regulatory compliance.
On top of least-privilege access control, MFA, SSO, and native online threat protection, GoodAccess now boosts your security with device posture check and forced always-on, preventing unsecured devices from entering your SDP and ensuring protective measures remain in place around the clock.