How to protect your and your company’s data in cyberspace? Let’s take a look at the three main areas of cybersecurity, the most common threats, and the steps you can take to protect your data in today’s age of information.
The importance of cybersecurity
Companies today are relying more and more on SaaS and cloud services. Data and systems have to be accessible from all around the globe, as the employees and colleagues make more use of the possibility of remote work. Governments, albeit a bit slow, pass laws and regulations like GDPR to protect personal data. This gradually shifts more and more of your data and communication online into cyberspace, introducing new challenges for your security. You cannot rely only on a strong password to keep your data safe. So what are the new challenges your company faces today?
The landscape of cybersecurity
There are three main areas of cybersecurity: device security, network security, and business systems security.

Device security
When talking about device security, this means the protection of everything that happens on your devices, such as a laptop, smartphone, or tablet. The most typical threats are malware, phishing, and ransomware. The aim of an attacker using these threats is usually to obtain sensitive data located on your device or to cause damage to it.
The typical solution for device security is antivirus software. It’s a great option for all your devices, as it takes care of a great deal of threats that might pass by your device. Good antivirus software also prevents unknown software from being installed without your knowledge.
Network security
It is when you connect to the internet, when network security kicks in. Among the most common threats are DDoS attacks, data breaches, and cyber espionage.
Let’s imagine the following situation: You’re on a business trip and have to review data about your client in the company’s CRM system. You connect to the public Wi-Fi hotspot available at the airport, connect to the company CRM system, and check the data. Easy, right? What you don’t (and usually can’t) see is who else is listening to your communications and intercepting the data you access. This is one of the possible ways a serious data breach might occur.
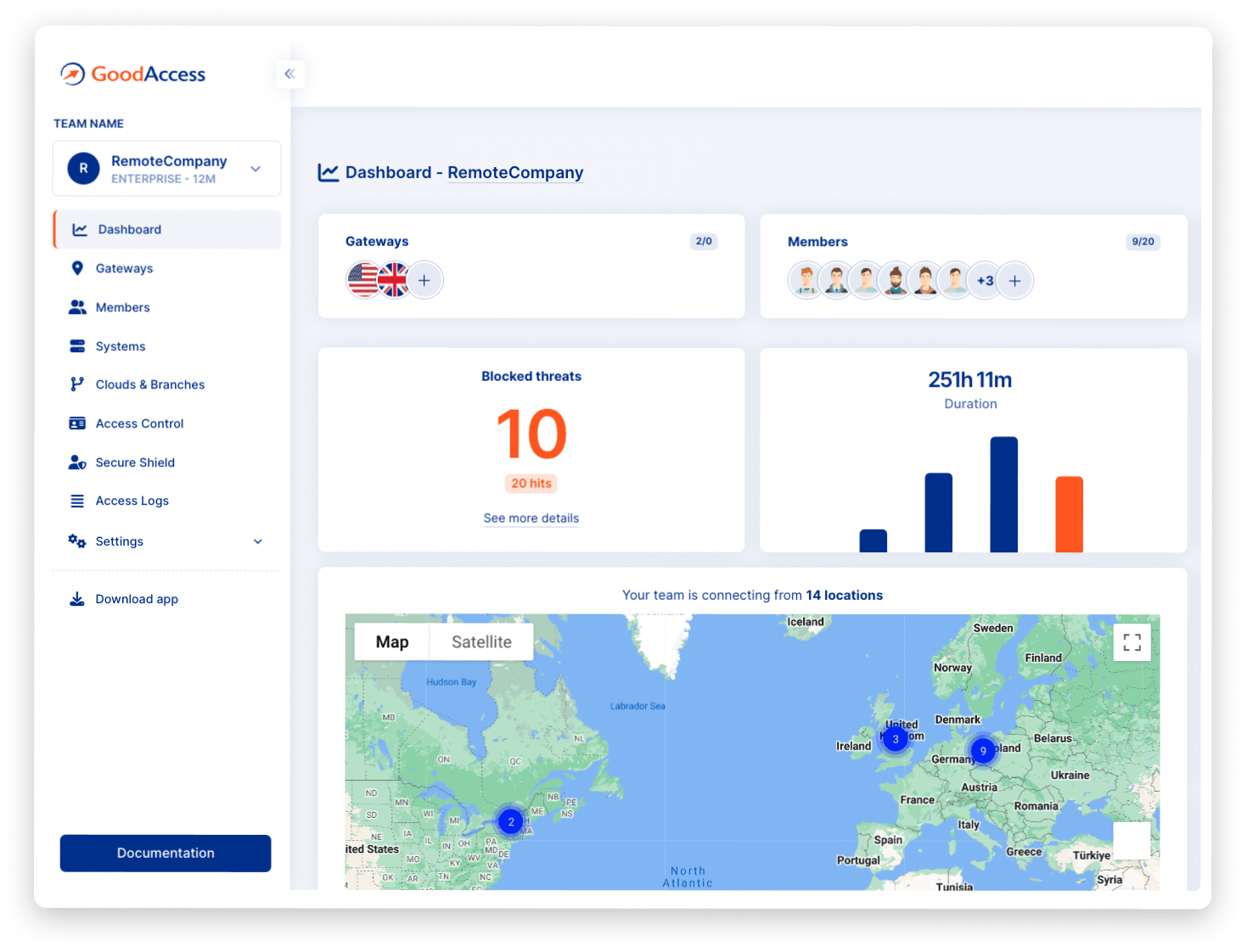
The best way to make your connection with company systems safe and encrypted is using GoodAccess. It’s a modern SASE solution that combines 6 main principles to protect your network:
- Zero Trust Network (ZTN)
- Global Software Defined Perimeter (SDP)
- Strong Network Encryption
- 2FA/MFA on the Network Layer
- Identity & Access Management (IAM) on the Network Layer
- Access Logs & Reports
Simply put, these principles ensure that you know exactly who you let into your network and what systems that user can access. Once you or your employees connect to the GoodAccess gateway, you get to work inside your company’s own private network and no outside party can intercept your communication. A secure island, safe from the sharks circling around.
Business systems security
The area of business systems security is concerned with anything that happens when you use your company’s business systems. The usual threats are session hijacking, unauthorized system access, and weak passwords. The goal of an attacker is quite similar to device security – to obtain sensitive data. However, unlike individual devices, business systems usually hold a lot more data – so the protection of company’s systems should be taken very seriously.
You can implement several principles to protect your company’s systems: IAM on the application level, 2FA/MFA reports from each system, whitelisting, or a strong password company policy. But the best option is to rely on all of those principles in combination with GoodAccess. Why? Because it also covers your business systems security, as it already uses features such as IAM and MFA on the network level.
How to protect yourself in cyberspace?
As we have seen, the best option is to rely on modern technology. Employees’ education also plays an impactful role, but it can’t prevent every possible threat. Unfortunately, there is no 100% attack-proof solution that can be used. However, you can get as close as possible by combining two modern solutions: antivirus and GoodAccess. This covers the three main areas of cybersecurity, and you can be at ease knowing your data are safe.
Upgrade your cybersecurity with GoodAccess.
Start your free 14-day trial today.