During the COVID-19 pandemic, many employees started working from home. One study shows that, following the rise of remote workers, 20% of organizations experienced security breaches.
With work-from-home trends such as employees making use of unsecured Wi-Fi networks at coffee shops, businesses need to rethink their approach to cybersecurity.
In this article, we look at the importance of cybersecurity for remote workers and offer advice on protecting your organization from security breaches.
Table of contents
Why Is Cybersecurity Important for Remote Workers?
8 Cybersecurity Tips for Employees
How to Keep Your Business Safe
Why Is Cybersecurity Important for Remote Workers?
Remote workers can work from different locations such as coffee shops and malls, and they communicate with team members online rather than in person.
This places them (and their devices) beyond the reach of traditional security measures their company provides on office premises. Consider the risks below that were chosen for their particular relevance to remote employees.
Unsecured Wi-Fi
Employees logging in remotely via unsecured Wi-Fi (at home, in a café, or a co-working space) run the risk of data exposure during transit.
Hackers are on the lookout for sensitive payloads that can be intercepted, and they use a variety of techniques, like man-in-the-middle-attacks. Such attack techniques allow them to steal access credentials or hijack sessions to steal the content of communication.
Online scams
Another highly present threat to remote workers are various kinds of online scams. Most commonly, these include phishing and variations on this attack.
Phishing messages, typically emails, manipulate employees into clicking malicious links or weaponized attachments. These can contain malware or take the victim to a spoofed site tricking them into giving up their access credentials and providing the scammer with a means of accessing company data.
The sinister side of phishing is in its reliance on social engineering. The messages can be highly personalized, so the victim is often unaware they are interacting with a malicious actor.
Sophisticated phishing attacks, aimed at senior executives (known as executive phishing or whaling), can cost millions in damages, such as during an incident in 2013, when a Taiwanese hardware supplier started sending fake invoices to Google and Facebook, which eventually totaled $122 million. Their finance department assumed that these invoices were legitimate and they made the payments on time.
Remote employees have a harder time checking the legitimacy of such requests without personal contact with co-workers.
Poor cyber hygiene
Hackers have also realized that small businesses are easy targets because they don’t always invest in cybersecurity. Their employees aren’t sent to seminars about online security, and they generally don’t have top-range security software installed on their devices.
To prevent large financial losses, lawsuits, and reputational damage, businesses need to provide remote workers with special training to protect themselves against online threats.
8 Cybersecurity Tips for Employees
If businesses want to prevent huge financial and reputational losses, they need to make sure that their remote employees are equipped to deal with cyberattacks.
If you work remotely, or your team works remotely, have a look at the tips provided below on how to prevent criminals from taking advantage of your unique work setup.
1. Use strong passwords
It seems obvious that you should have a strong password–especially since this is encouraged everywhere. However, in 2022, it was determined that “password” is still the most common password, followed by “123456”, “guest”, and “qwerty”.
A remote employee who uses these passwords to access their work files or chats is making life easy for hackers. They simply need to use their email account—which may already be available on your business's website—and test the most common passwords (this is known as a dictionary attack).
If they gain access, they can manipulate invoices and banking details, leading to huge losses for your organization. It could also allow them to drop additional malware, such as ransomware, and encrypt all your systems and data, effectively crippling your organization unless you pay the demanded ransom.
There are three steps you can take to ensure that remote employees have strong passwords that won’t be cracked:
- Install a password manager: Many password managers online offer free protection. You simply need to install the program, which usually has a browser extension, and it will encrypt and save all your passwords. Depending on the manager you choose, you may also receive suggestions for strong passwords that will eliminate vulnerabilities.
- Implement regular password changes: Set up your security permissions so that you and your team have to regularly change your passwords. If it’s not possible to set this up automatically with the applications and devices your remote workers use, then add reminders to your calendar and have days dedicated to changing all the company passwords.
- Set up company rules and regulations: You need to make it clear that proper password management is serious business at your organization. It’s vital that you clearly outline what remote workers should and should not do. For example, you can have a rule against sharing passwords in group chats.
Unless your employees understand the consequences of having exposed passwords, they won’t feel compelled to follow your suggestions.
Ensure your business has regular training sessions on password protection and go through case studies of other businesses that went bankrupt after hackers took advantage of weak passwords.
2. Use the SLAM method to identify suspicious emails
In 2019, government employees in Puerto Rico were tricked into sending $2.6 million to hackers in a spear phishing incident.
The bad actors contacted employees from different departments and told them that they urgently had to update the bank details of particular suppliers. Without the necessary knowledge to recognize this as a cyberattack, two employees followed through with the request.
Suspicious emails are easily disguised as legitimate communication. Hackers sometimes even use the company’s official branding and address the recipient in a tone that’s similar to previous email exchanges.
You can teach your remote workers how to spot phishing emails by using SLAM. This is an acronym that stands for Sending, Links, Attachments, and Messages. Have a look at what each of these refers to:
- Sending: The first step is to assess the “sending” or “from” email address. Bad actors often try to trick you into thinking that you’re receiving an email from a legitimate source. For example, they may use an “r” and “n” next to one another to give the appearance of an “m” (“rn”). Before you open an email, make sure that you recognize the sender and carefully check for errors.
- Links: Hackers often include links in emails that lead you to a fake website that steals your credentials. For example, you may receive an email informing you that you need to update your Microsoft Teams password. However, if you click on the link, you will get sent to a knockoff site that captures your login details. Before clicking on a link, you should verify its validity. In our Teams example, your best action would be to manually open Microsoft Teams and check whether you need to update your password. In other cases, hover over the link and check if it points to a site you recognize.
- Attachments: If you click on a malicious attachment, it can install malware on your device and, ultimately, compromise the security of your data. Even if you’re certain that you recognize a sender, you should still be cautious about clicking on attachments. It’s a good idea to scan suspicious attachments with your security software to ensure that it doesn’t contain any harmful files.
- Messages: It may be difficult to spot a spear phishing or whaling email because it’s usually personalized to the receiver. However, general phishing emails are often riddled with errors, such as spelling mistakes and strange phrases. You should also be cautious of emails that “require your urgent attention”. Con artists often pretend to be representatives from local tax authorities or payment platforms, claiming that you owe them money or that there was a payment error.
If every email is stress-tested by SLAM, you will have less to worry about while your employees work remotely.
3. Install software updates as they become available
New threats appear on the Web every day. Fraudsters are constantly testing new tricks that might help them obtain your personal data. This means that companies should regularly update their operating systems, tools, and antivirus software to include the latest protection against cyberattacks.
For example, if bad actors release a new piece of malware or exploit an unknown vulnerability in popular software, your security tools will quickly find a way to block the new threat or and vendors will patch the vulnerability. You will then have to update your app, device, or browser to implement the new protection.
However, if you neglect these updates, you will miss out on the latest security software and you may put yourself and your company at risk.
4. Implement multi-factor authentication
A con artist may be able to manipulate you into sharing your login details with them, but they won’t be able to access anything if you have multi-factor authentication. This is when you set up an account to verify your identity with a separate device—usually a mobile one.
Multi-factor authentication sends a one-time password (OTP) to your verification device, which you then enter after your login details. If you unexpectedly receive an OTP it could be a sign that a fraudster has your password.
You must never share these codes with anyone. In some cases, hackers call their victims pretending to be authorities and they request the OTPs that they’ve allegedly sent to their devices.
5. Secure your Web browser
While browsing the Web, you will use sites that request personally identifiable information, such as your address for delivery purposes or your login details to your personal blog.
This means that, if your browser is compromised, you may be handing over sensitive information to criminals.
The first step to a secure browser is to make sure you’re using a well-known browser brand. In general, Google Chrome, Firefox, and Microsoft Edge are trustworthy browsers. Before using a lesser-known browser, make sure you do some research on it.
Once you know you’re working with a trusted browser, you need to make sure that it doesn’t store any sensitive information. You should disable the following:
- Autofill: It may feel time-consuming to add the same information to a website several times. However, you’ll have a much bigger headache if your personal information is stolen. For example, it’s essential that you prevent your banking details from being saved for the sake of easily autofilling later on. It’s okay to have specific websites, such as Takealot or Uber, save your banking details. But you shouldn’t save them on your browser.
- Saved passwords: It may seem convenient to save your passwords directly to your browser. However, it’s usually safer to save them on your password manager, as it offers a higher level of encryption. You will still be able to have your passwords autofill, but the data will be drawn from your manager and not your browser.
Ultimately, remote workers should be cautious when trusting their browsers with sensitive information, because it’s more likely to be hacked than an app that specializes in security.
6. Encourage employees to speak up if they notice something suspicious
One of the sore points of working remotely is a lack of communication. The majority of companies take steps to ensure that team members can easily connect with one another, usually through programs such as Slack and Zoom.
Unlike an office environment, where employees easily share information, remote workers may be less likely to notify their colleagues of a seemingly harmless threat. You need to make sure that any suspicious activity—regardless of how small it may appear—is immediately reported to the whole team.
You can create a specific channel where employees can put up screenshots of unusual emails so that the whole team can immediately be aware of any potential threats.
7. Use a VPN
Remote workers connect to company resources via Wi-Fi at home, in a coworking space, or a coffee shop. These are public networks, and the company has no control over them.
This places the remote workers and the data they exchange with the company in a vulnerable position. Cyberattackers may intercept their data, steal it, tamper with it, or mis-use it to gain access further into the company infrastructure.
Virtual private networks (VPN), provide the much needed security and anonymity in such scenarios.
VPNs create an encrypted tunnel between the remote user’s device and the target system, which effectively conceals the traffic from the prying eyes of cybercriminals and shields it from tampering.
This enables secure data transfers, which is important for users who handle sensitive data or log in to a local system from a remote location.
Business VPNs, in particular, are VPN solutions targeted at the needs of organizations. They don’t just provide safe web browsing, but come with additional security and networking functionalities that enable secure remote work for multiple users.
8. Adopt ZTNA
Organizations with a long-term reliance on remote workforce should look into more robust and scalable methods of making remote work secure and practical.
One such approach is zero-trust network access (ZTNA).
ZTNA grants access based on identity and context instead of network boundary. This means that remote employees are rigorously verified every time they access resources.
The ZTNA approach may be more than just a quick tip, but the transition will be worth it. Companies that implement ZTNA will benefit from
- Increased cyber resilience—Access is granted on the least-privilege principle, which dampens the impact of potential breaches.
- Scalable remote access—A dedicated access management platform easily adapts to changing demands, ensuring seamless connectivity for remote employees.
- Centralized granular access control—Granular centralized access control allows you to define precise rules and policies to further shrink your organization’s attack surface.
- Greater cybersecurity compliance—Access controls combined with account activity monitoring helps meet regulatory standards.
How to Keep Your Business Safe
Remote employees—especially those who work for small businesses—are at risk of being targeted by cybercriminals.
There are many ways to improve their online safety and protect the businesses they work for. This includes safe password management, using multi-factor authentication, using a VPN when on public Wi-Fi networks, and deploying access management platforms like ZTNA.
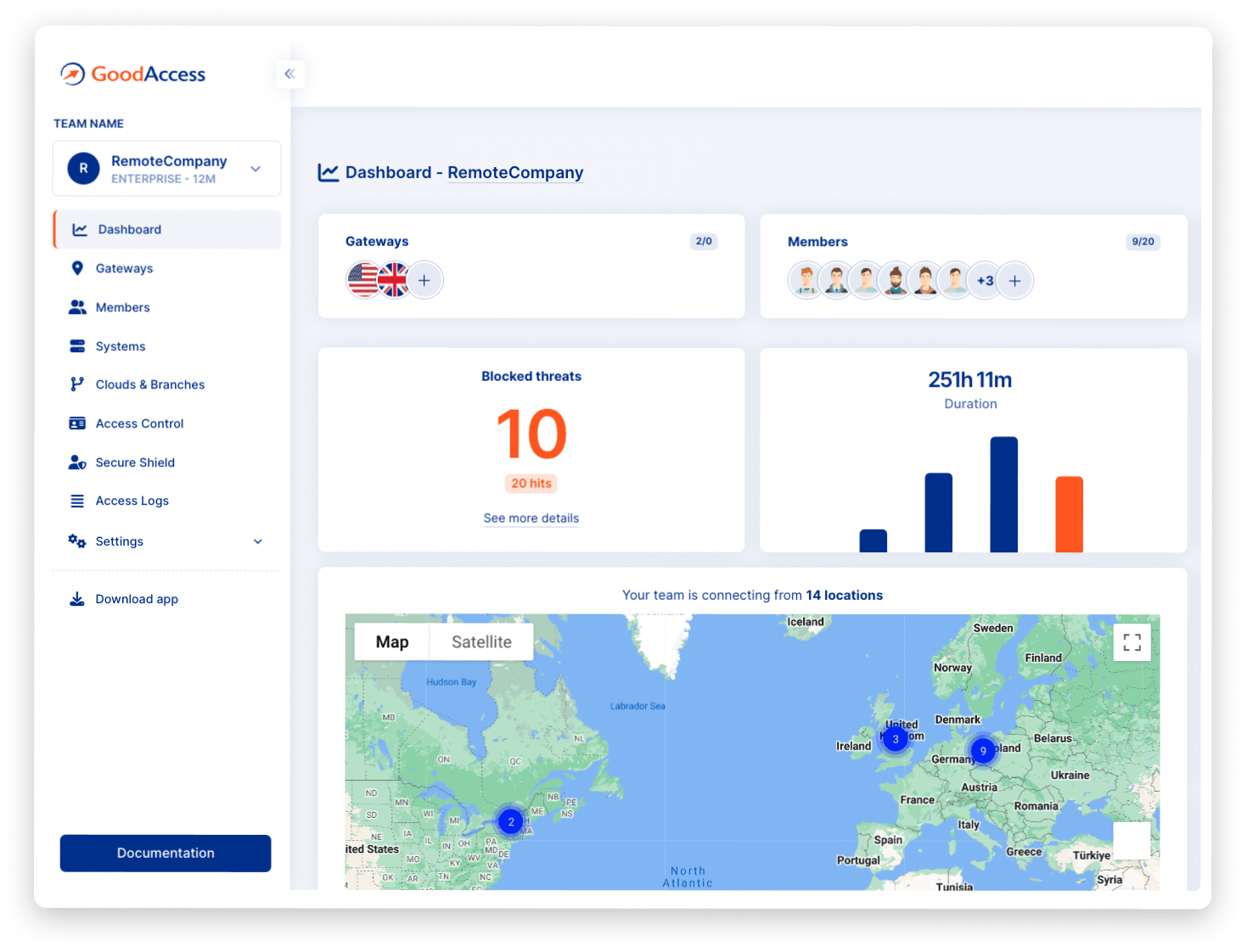
GoodAccess, a company trusted by over a thousand businesses worldwide, specializes in VPN security and zero-trust network access.
You can start with a free 14-day trial to see whether it’s the right service for you and your remote workers. This includes a range of services, such as public Wi-Fi protection and encrypted Internet access.